Gallery Photos

Through Door Kitchen Cabinet Designs
It also acts as a serving area for the dining room — and even a patio — with easy access from thekitchen. Want to close out the conversation going on in the family room while you have your own in thekitchen? A pass-throughprovides that option as well. Here are some pass-throughsthat look great, provide options and function like a dream.
View Gallery & Article
G Router Network Setup For Small Business
This guide will help you tosetup asmallbusinessnetwork, including your switches,routers, and wireless solutions.
View Gallery & Article
Modern Kitchen Cabinets With White Shaker Doors
Explore affordableshakerkitchencabinets, our most popularkitchenstyle at IKEA! Timelessshakerdoorswork in traditional, contemporary &modernkitchens.
View Gallery & Article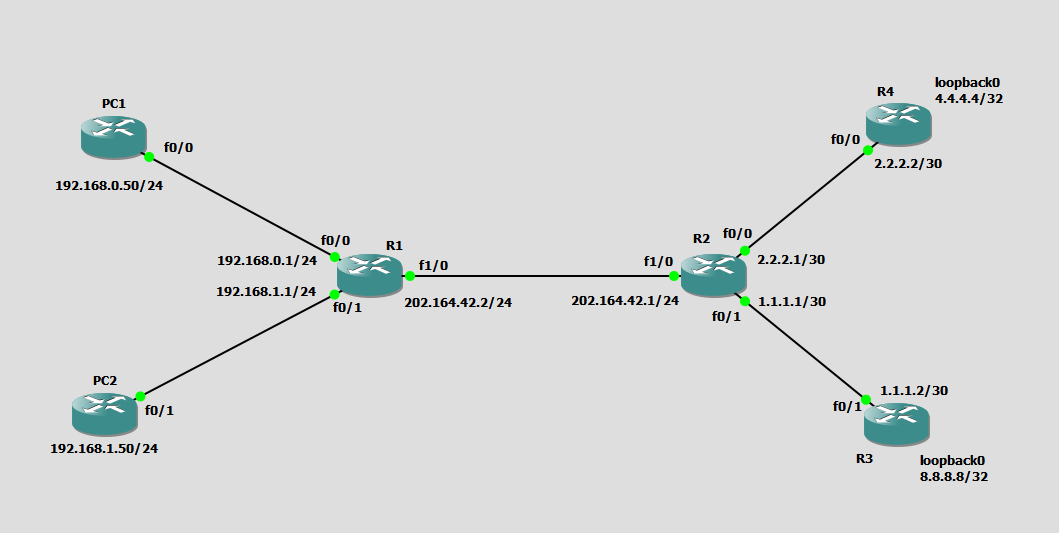
Network Router Configuration Ip Address
Here are three of the most useful. Find YourRouter'sIPAddresswith Command Prompt, PowerShell, or Windows Terminal Yourrouter'sIPaddressis the "Default Gateway" in yournetworkconnection information on Windows. If you prefer using the Command Prompt, you can find the default gateway for any connection quickly by using the ipconfig command.
View Gallery & Article
Mental Health Support Chat Room Online
Freeonlinecounseling from trained volunteer listeners, andonlinetherapy by licensed therapists. Feeling overwhelmed? You deserve to feel your best.ChatNow
View Gallery & Article
G Router Setup For Network Analytics
5) Connect a device to your new WiFinetworkOnce yourrouteris configured and connected to ournetwork, you can connect a device to the WiFinetwork. The WiFinetworkname or SSID and the default password are printed on the sticker on the back of your newrouter.
View Gallery & Article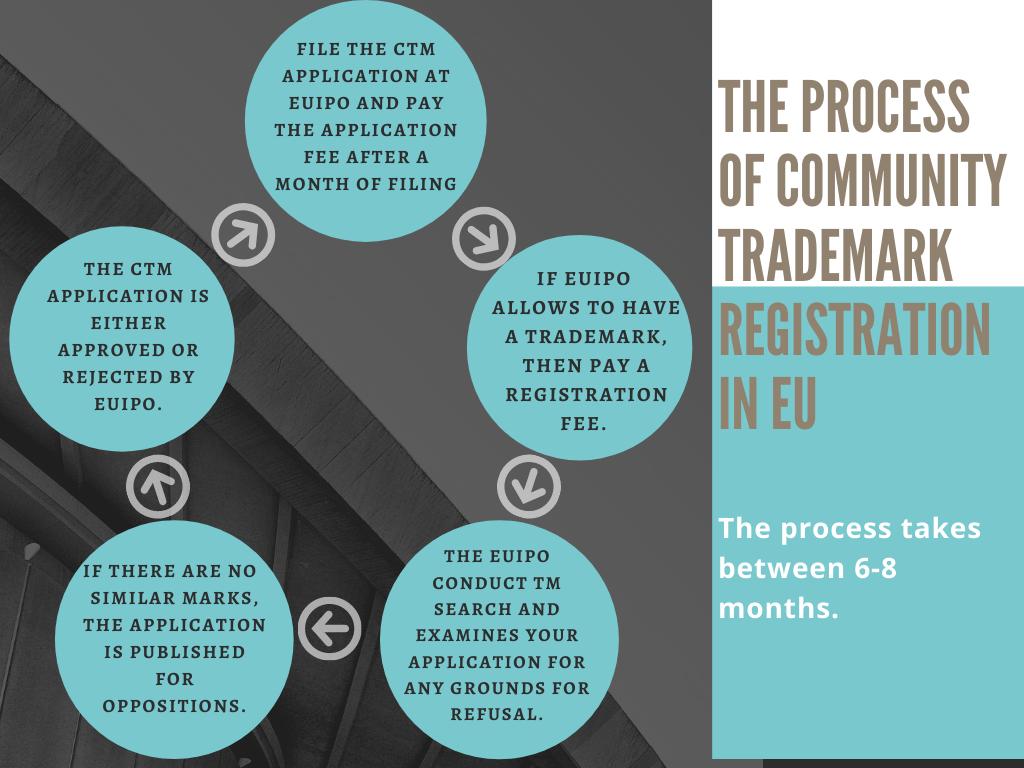
Trademark Search Procedures Europe
EUIPO is the European Union Intellectual Property Office responsible for managing the EUtrademarksand the registered European Union designs, and EU geographical indications for craft and industrial products.
View Gallery & Article
Gutter Guard Installation For Gutter Guards With Attachments
Aug 8, 2025Learn how to installgutterguardswiththis comprehensive step-by-step guide covering types, tools,installation, and maintenance tips.
View Gallery & Article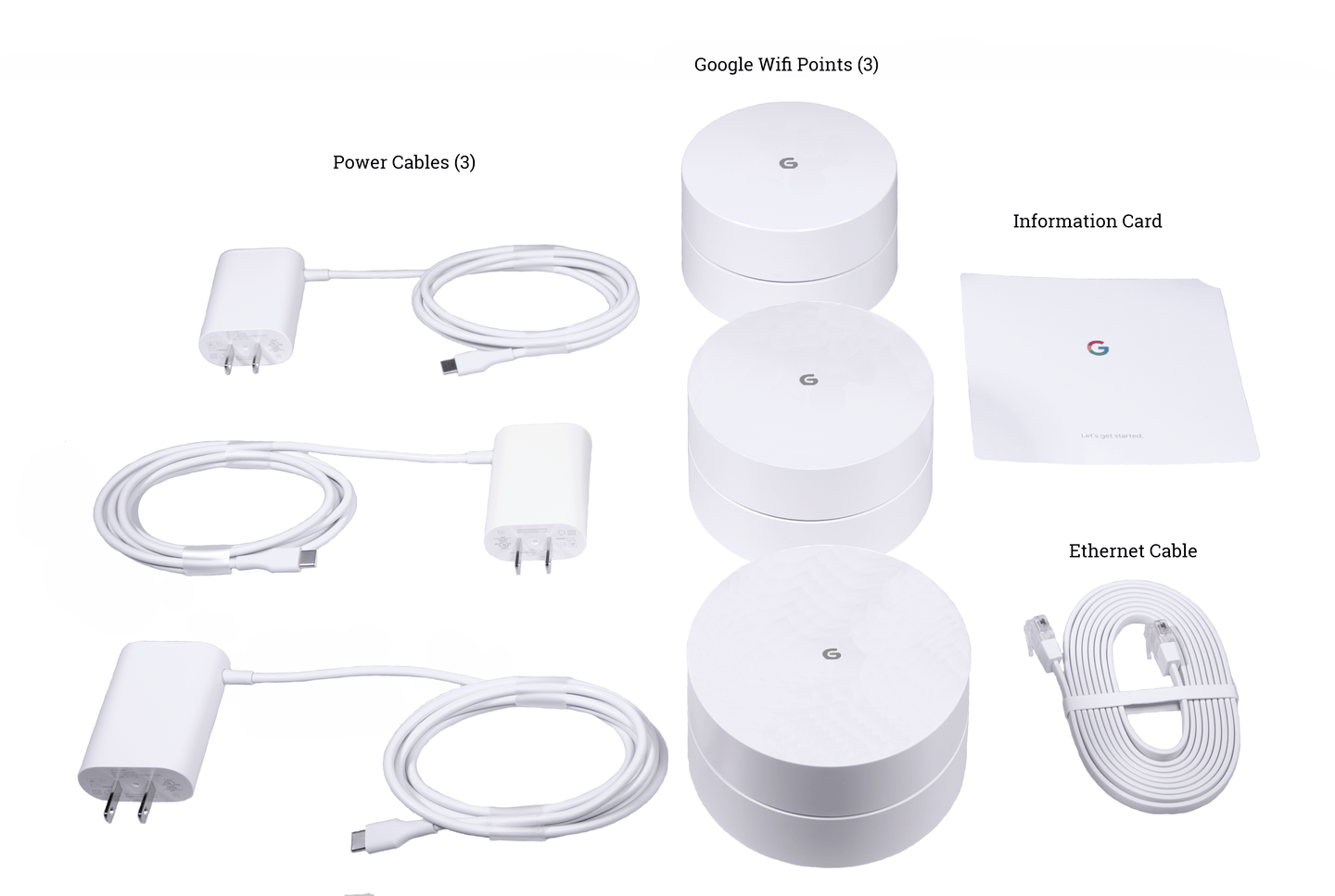
Google Wi-Fi Setup For Extortion Types
Mar 7, 2026Key PointsWi-Finetworks are vulnerable to various hacks like MITM, brute force, and phishing, which can result in stolen data or disrupted services. Using strong encryption methods, VPNs, and digital certificates significantly reduces the risk of unauthorized access toWiFinetworks. The SecureW2 JoinNow PKI and Cloud RADIUS solutions offer passwordless authentication, enhancing enterprise ...
View Gallery & Article