Configuring G Wireless Network for Network Access Control
As businesses continue to rely heavily on wireless networks for connectivity and performance, configuring a G wireless network for network access control has become increasingly important. This is especially true in today's digital landscape, where security threats are on the rise and network security is a top concern for organizations. In this article, we'll explore the importance of network access control, how to configure a G wireless network for network access control, and best practices for ensuring a secure and efficient network.
Understanding Network Access Control
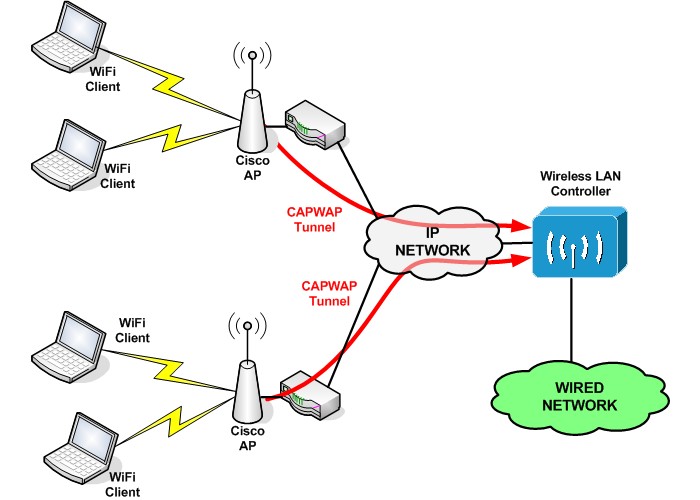
Network access control (NAC) is a key component of network security that allows organizations to regulate and manage user and device access to their network. This includes identifying and controlling user identity, network connectivity, and device compliance. NAC helps to prevent unauthorized access, limit network sprawl, and improve overall network security.
- Network access control (NAC) is a security mechanism that regulates access to a network.
- NAC helps to prevent unauthorized access to a network, limiting network sprawl and improving overall security.
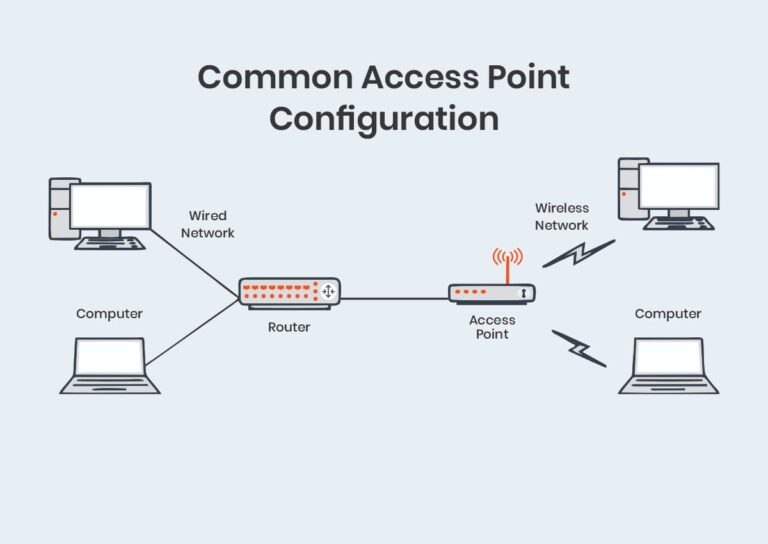
Configuring G Wireless Network for Network Access Control
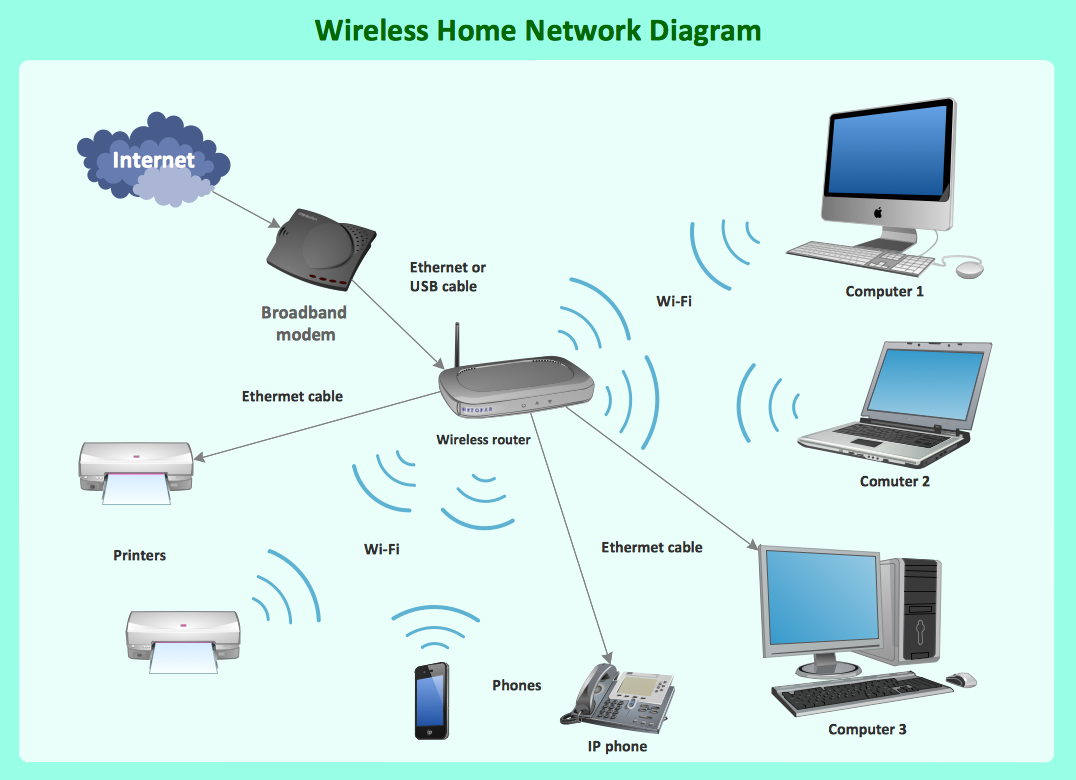
To configure a G wireless network for network access control, follow these steps:
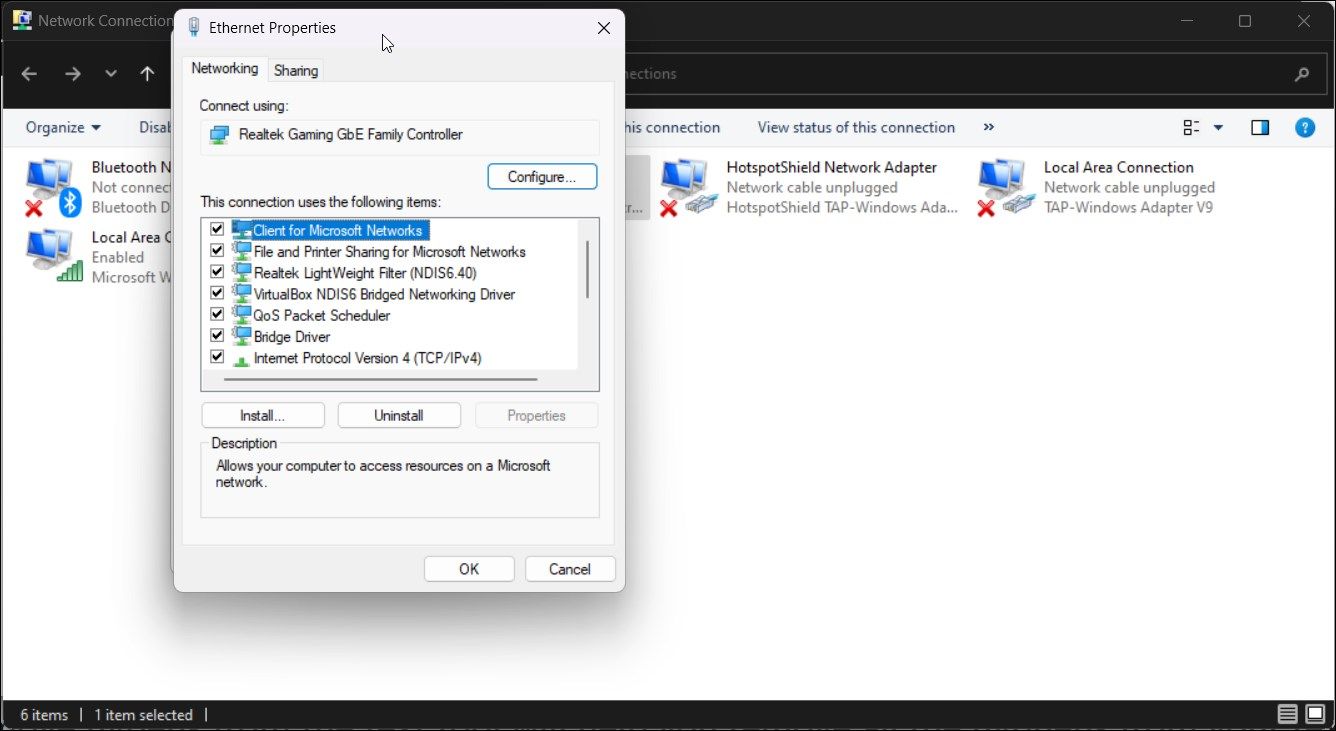
- Easily configure your WiFi network by signing into your GFiber account and accessing your router's settings for enhanced connectivity and performance.
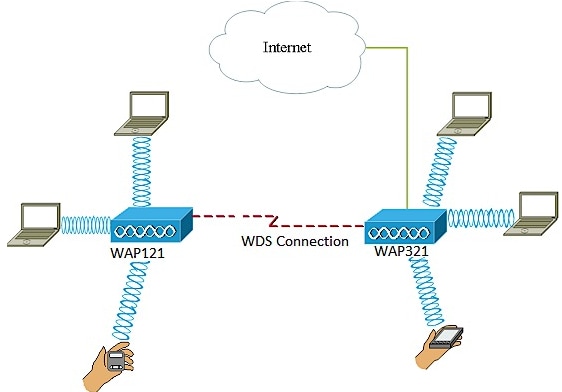
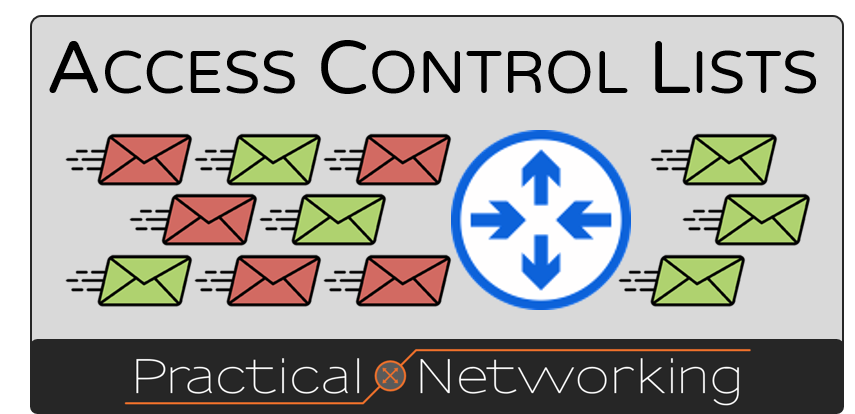
- Create a separate guest network or configure Access Control List (ACL) rules for guest users. The access rules can be Unrestricted, Network-Based, and Role-Based.
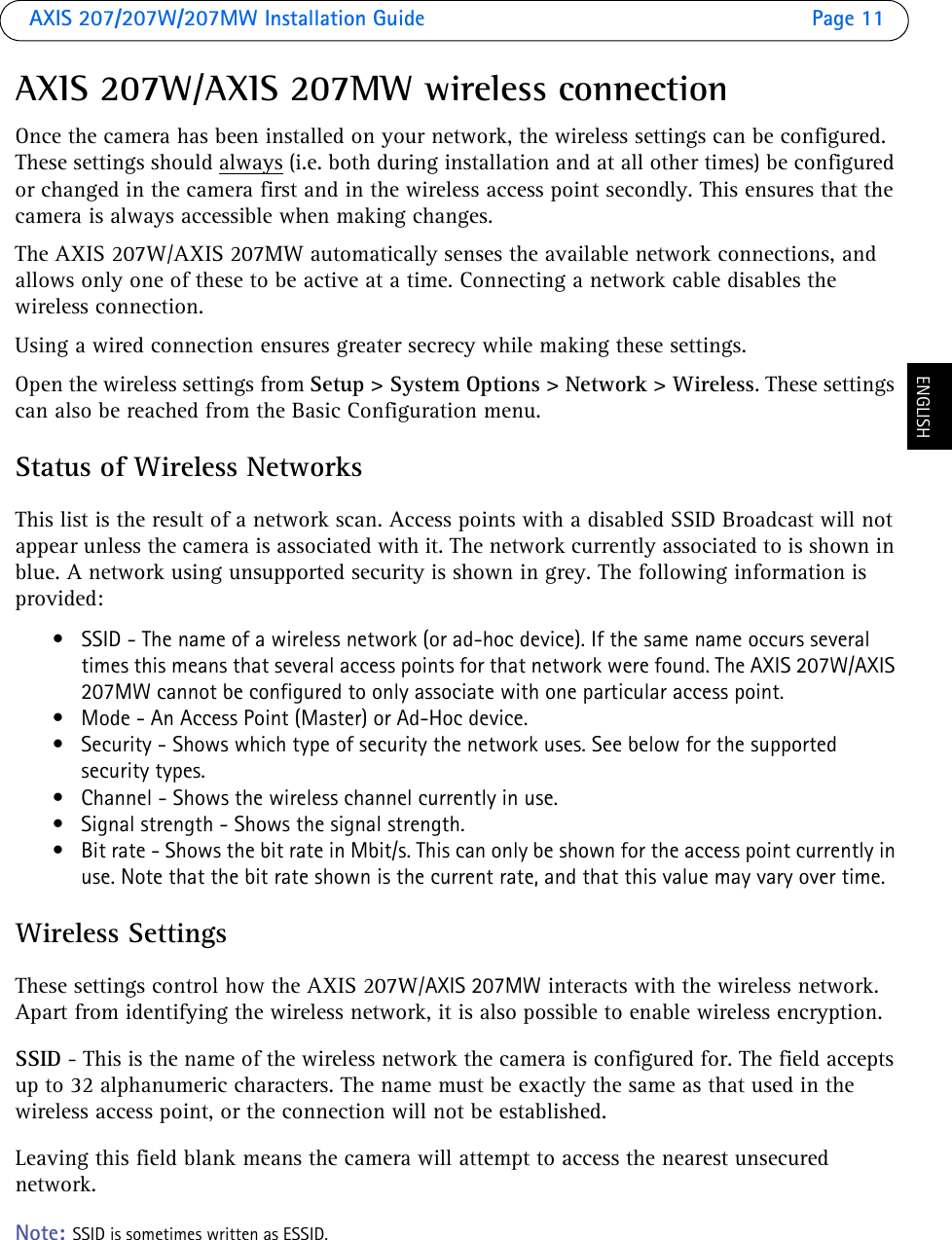
- Set up and manage your G.Network WiFi network using the Nokia WiFi app. Configure your broadband settings, parental controls, and limit internet access.
Best Practices for Configuring G Wireless Network for Network Access Control
Here are some best practices to consider when configuring a G wireless network for network access control:
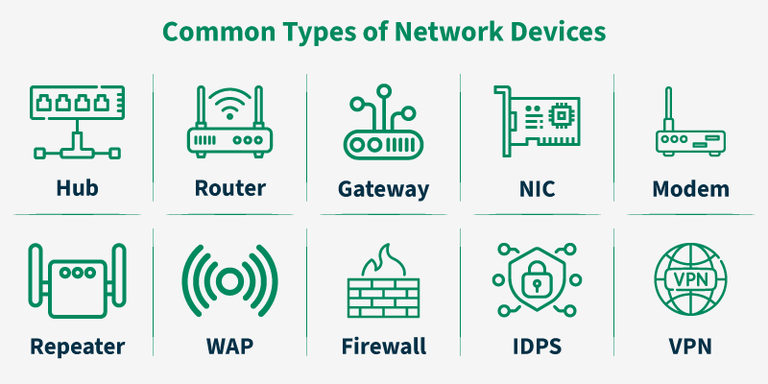
- Implement network segmentation to isolate sensitive networks and data.
- Use authentication protocols like 802.1X and SSL/TLS to secure network access.
- Implement access control lists (ACLs) to control incoming and outgoing traffic.
- Regularly update and patch network devices and software to prevent vulnerabilities.
- Use intrusion detection and prevention systems (IDPS) to monitor and block malicious activity.
Conclusion
Configuring a G wireless network for network access control is a crucial step in maintaining a secure and efficient network. By understanding network access control, configuring your G wireless network for network access control, and implementing best practices, organizations can limit network sprawl, prevent unauthorized access, and improve overall network security. Stay ahead of the threat landscape by staying up-to-date with the latest security best practices and staying ahead of emerging security threats.
Additional Resources
For further information on configuring G wireless network for network access control, consider the following resources:
- Linksys EA6300: Learn how to configure your wireless network modes, security settings, and access control options for optimal performance and security.
- Nokia G-2425G-A: View and download the quick reference manual for the ONT G-2425G-A wireless access point.