G Wireless Network Secure Data Sharing: A Comprehensive Guide
Introduction
The widespread adoption of wireless networks has revolutionized the way we communicate, work, and live. However, with the convenience of wireless connectivity comes the risk of data breaches and unauthorized access to sensitive information. In this article, we will delve into the world of G wireless network secure data sharing, exploring the best practices, technologies, and protocols that can help protect your network and keep your data safe.The Importance of Wireless Network Security
Wireless networks introduce additional security risks compared to their wired counterparts. Hackers can exploit vulnerabilities in wireless networks to gain unauthorized access to sensitive information, disrupt network operations, or even use your network as a launching pad for malicious activities. To mitigate these risks, it is essential to implement robust security measures to protect your wireless network and the data that flows through it.Key Technologies and Protocols for Secure Data Sharing
Several technologies and protocols play a crucial role in securing G wireless network data sharing. Some of the most important ones include:- Advanced Encryption Standard (AES): AES is a widely used encryption algorithm that provides strong protection for data transmitted over wireless networks.
- Wi-Fi Protected Access 2 (WPA2): WPA2 is a security protocol that uses AES encryption to protect data transmitted over Wi-Fi networks.
- Wireless Protected Access 3 (WPA3): WPA3 is the latest security protocol that provides enhanced protection for data transmitted over Wi-Fi networks, including individualized data encryption and optional secure key exchange.
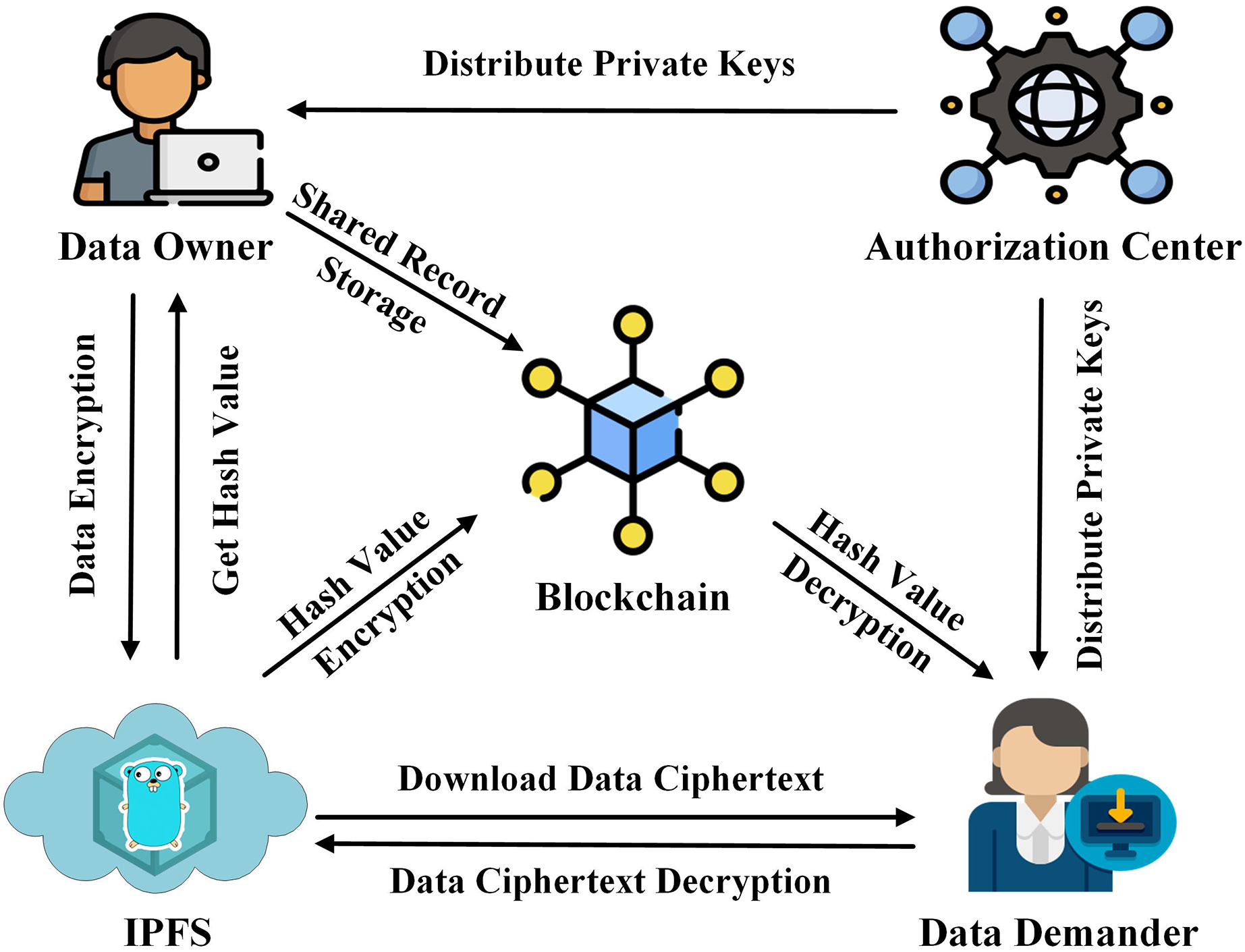
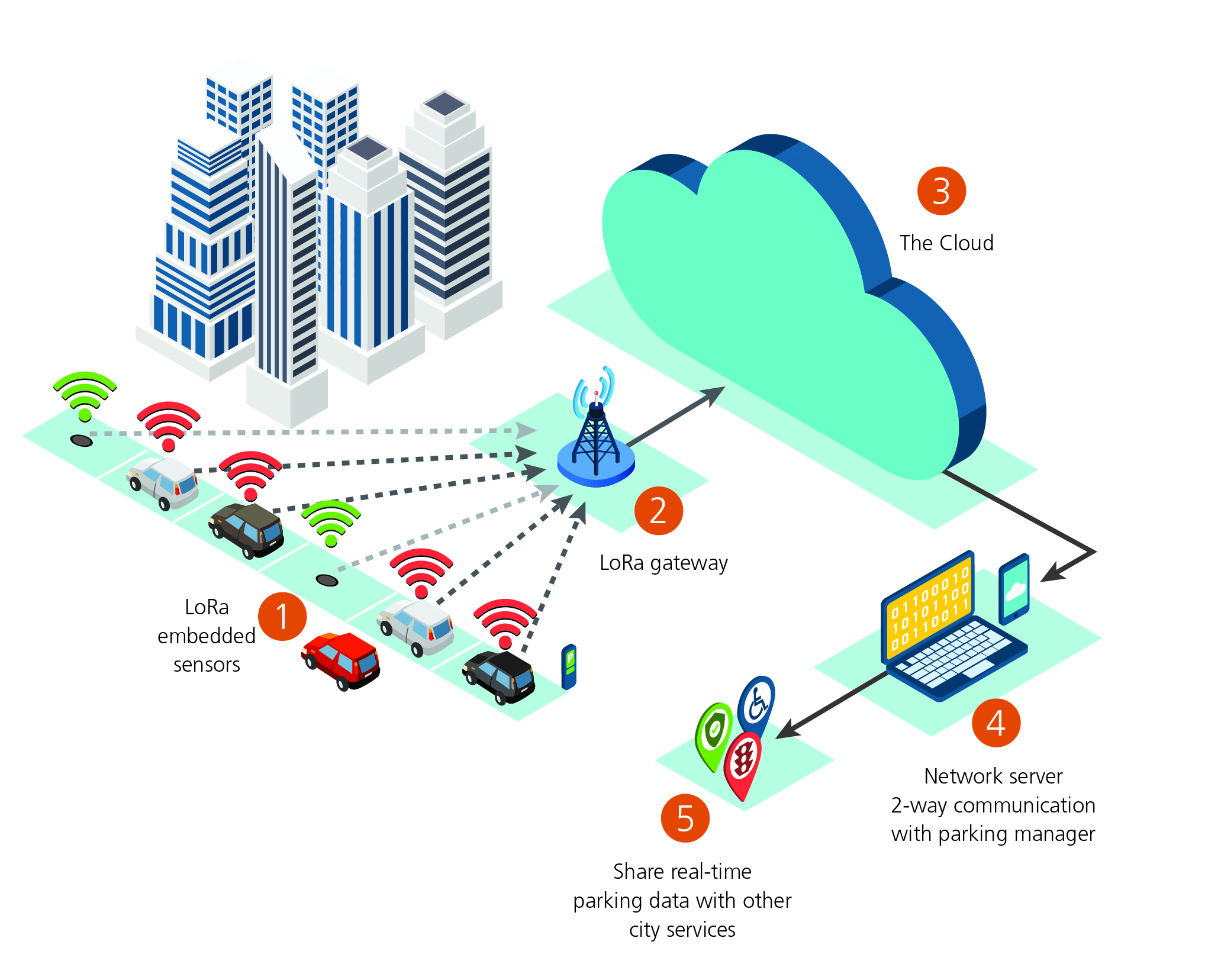
- Blockchain: Blockchain technology can be used to secure data sharing by providing a decentralized, immutable, and transparent way of storing and sharing data.

Best Practices for Securing G Wireless Network Data Sharing
To ensure secure data sharing over G wireless networks, follow these best practices:- Use strong passwords and passphrases: Use unique and complex passwords for your wireless network and devices to prevent unauthorized access.
- Enable WPA3 and AES encryption: Ensure that your wireless network uses WPA3 and AES encryption to protect data transmitted over the network.
- Regularly update your firmware and software: Keep your wireless network devices and firmware up to date to ensure that you have the latest security patches and features.
- Use a firewall and intrusion detection system: Implement a firewall and intrusion detection system to detect and prevent unauthorized access to your wireless network.
- Monitor your network activity: Regularly monitor your network activity to detect and respond to potential security threats.