Setting Up a G Network for Secure Access to Applications
As businesses increasingly move towards a distributed workforce, securing access to applications and resources has become more challenging. With the proliferation of remote work, the need for robust network security and access controls has become paramount.
What is G Network Setup for Secure Access to Applications?
G Network, now known as Microsoft Entra, converges network, identity, and endpoint access controls for secure access to any app or resource from any location, device, or identity. It enables and orchestrates access policy management for corporate employees.
Components of G Network Setup
- Microsoft Entra Internet Access
- Microsoft Entra Private Access
- Global Secure Access client
- Remote network connectivity
- Quick Access apps
Microsoft Entra Internet Access
Microsoft Entra Internet Access isolates the traffic for Microsoft applications and resources, such as Exchange Online and SharePoint Online. Users can access these resources by connecting to the Global Secure Access client or through a remote network, such as in a branch office location.
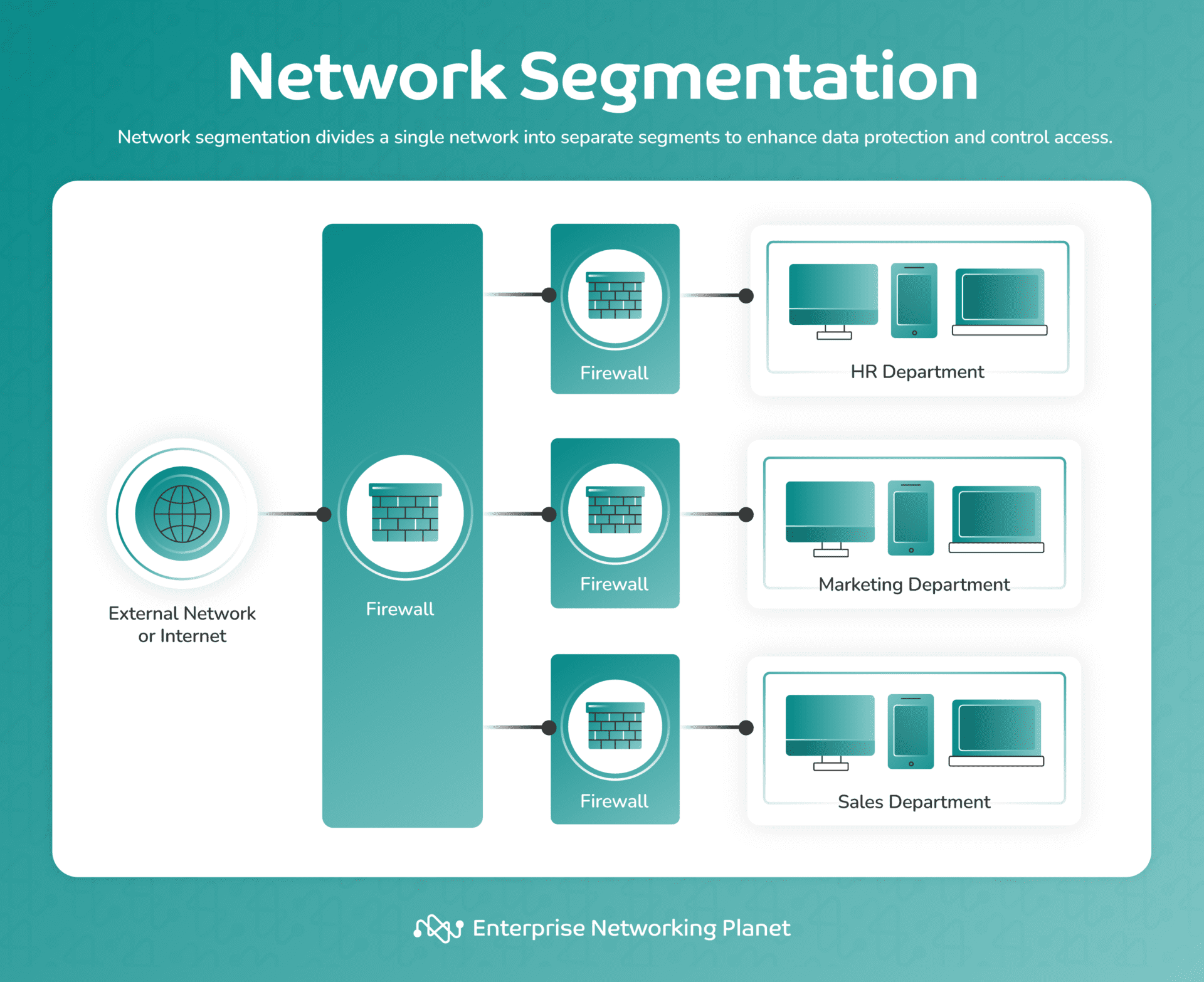
Microsoft Entra Private Access
Microsoft Entra Private Access is an advanced security solution that provides granular network access based on user needs. It enables users to access specific network destinations on their private network, and administrators can create private applications with precise segmentation and least privilege access.
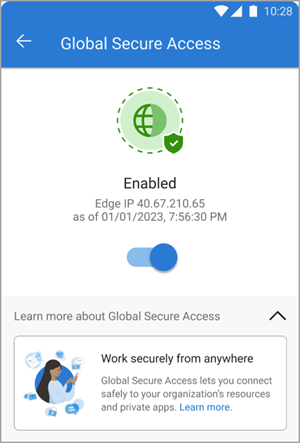
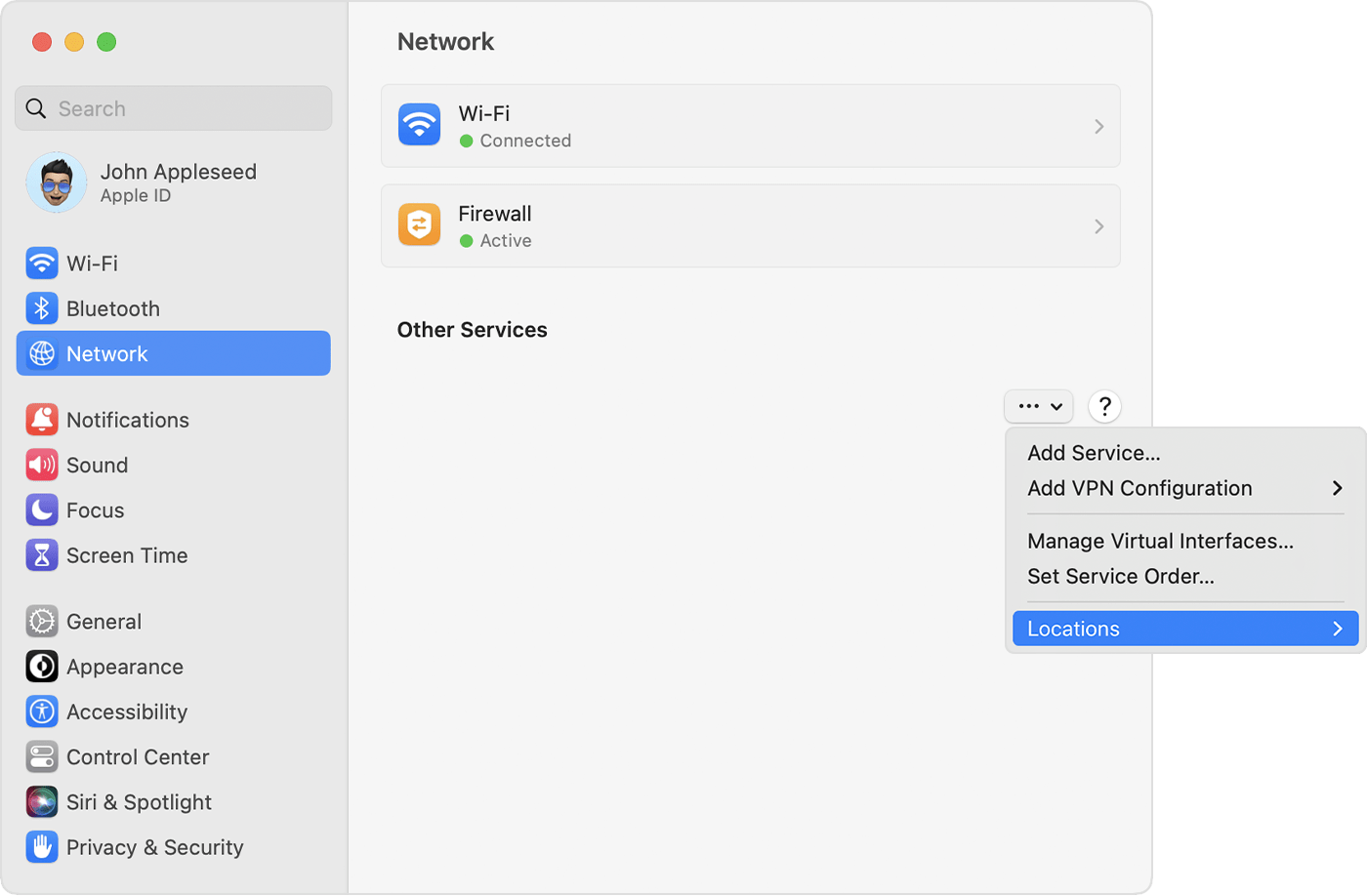
Global Secure Access Client
The Global Secure Access client secures network traffic at the end-user device. It can be downloaded and installed on Windows devices, and provides features such as web filtering policies and security profiles.
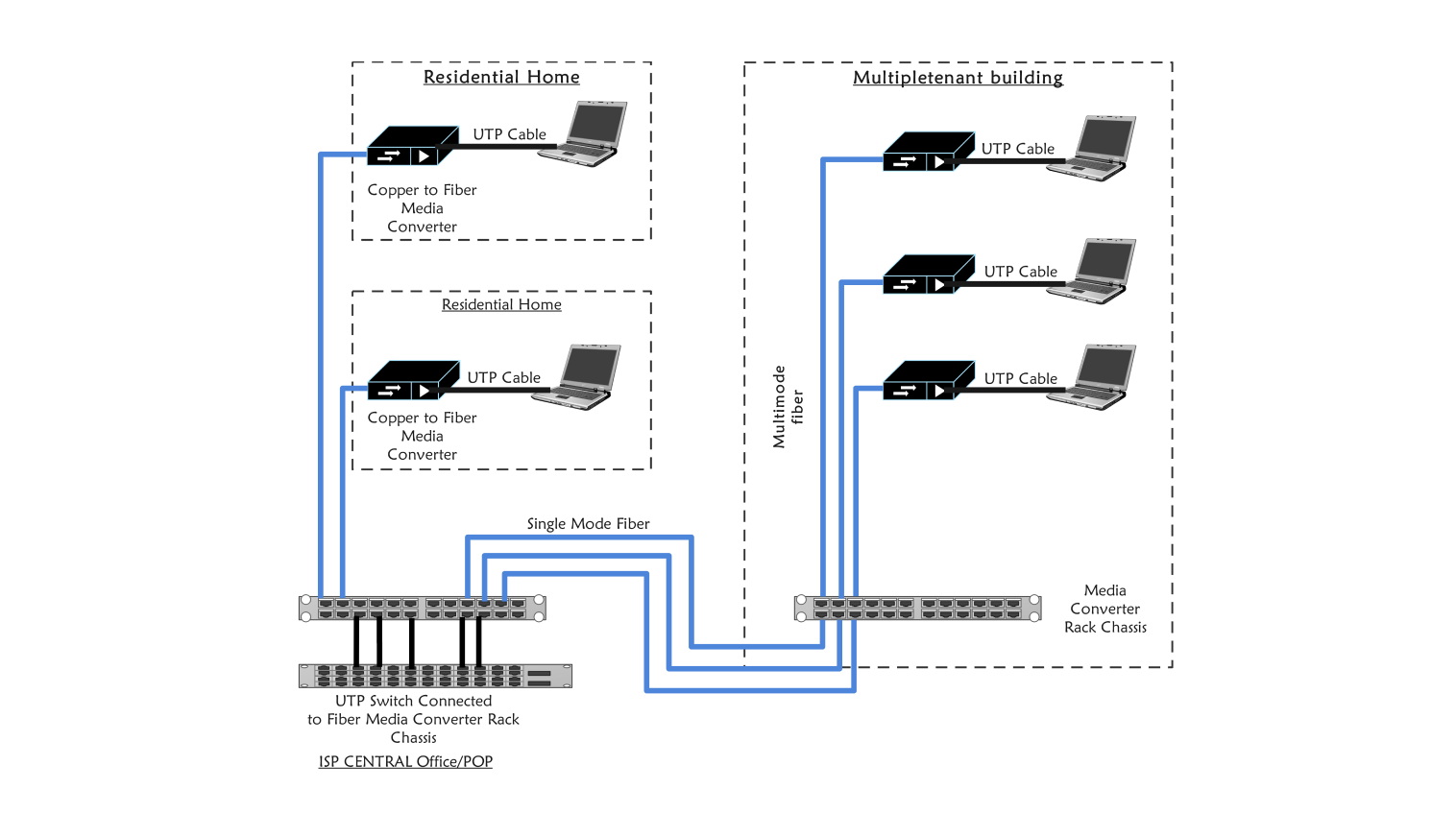
Remote Network Connectivity

Setting up remote networks connects users in remote locations to Global Secure Access. A remote network is configured, and a traffic forwarding profile is assigned to manage corporate network traffic. Global Secure Access provides remote network connectivity, allowing administrators to apply network security policies to outbound traffic.
Quick Access Apps
Quick Access apps provide users with secure access to internal resources without the need for a VPN or other complex access methods. They are created by administrators and can be customized to provide access to specific applications or resources.
Conditional Access Policies
Conditional access policies can be used to secure Quick Access applications, ensuring that only authorized users have access to sensitive resources. These policies can be based on user identity, location, device, or other factors.
Conclusion
A G Network setup for secure access to applications provides a robust and secure way for users to access resources from any location, device, or identity. By understanding the components of G Network, including Microsoft Entra Internet Access, Microsoft Entra Private Access, the Global Secure Access client, remote network connectivity, and Quick Access apps, administrators can implement a secure and efficient access solution for their organization.
Best Practices for Implementing G Network
- Implement strong access policies based on user identity, location, and device.
- Use conditional access policies to secure sensitive resources.
- Configure remote network connectivity to apply network security policies to outbound traffic.
- Use Quick Access apps to provide secure access to internal resources.
- Monitor and review Global Secure Access logs to ensure security and compliance.
Benefits of G Network
The benefits of implementing a G Network setup for secure access to applications include:
- Improved network security and access controls.
- Reduced risk of data breaches and cyber attacks.
- Enhanced compliance with regulatory requirements.
- Increased productivity and efficiency for users.