G Network Configuration for Malware Protection: A Comprehensive Guide
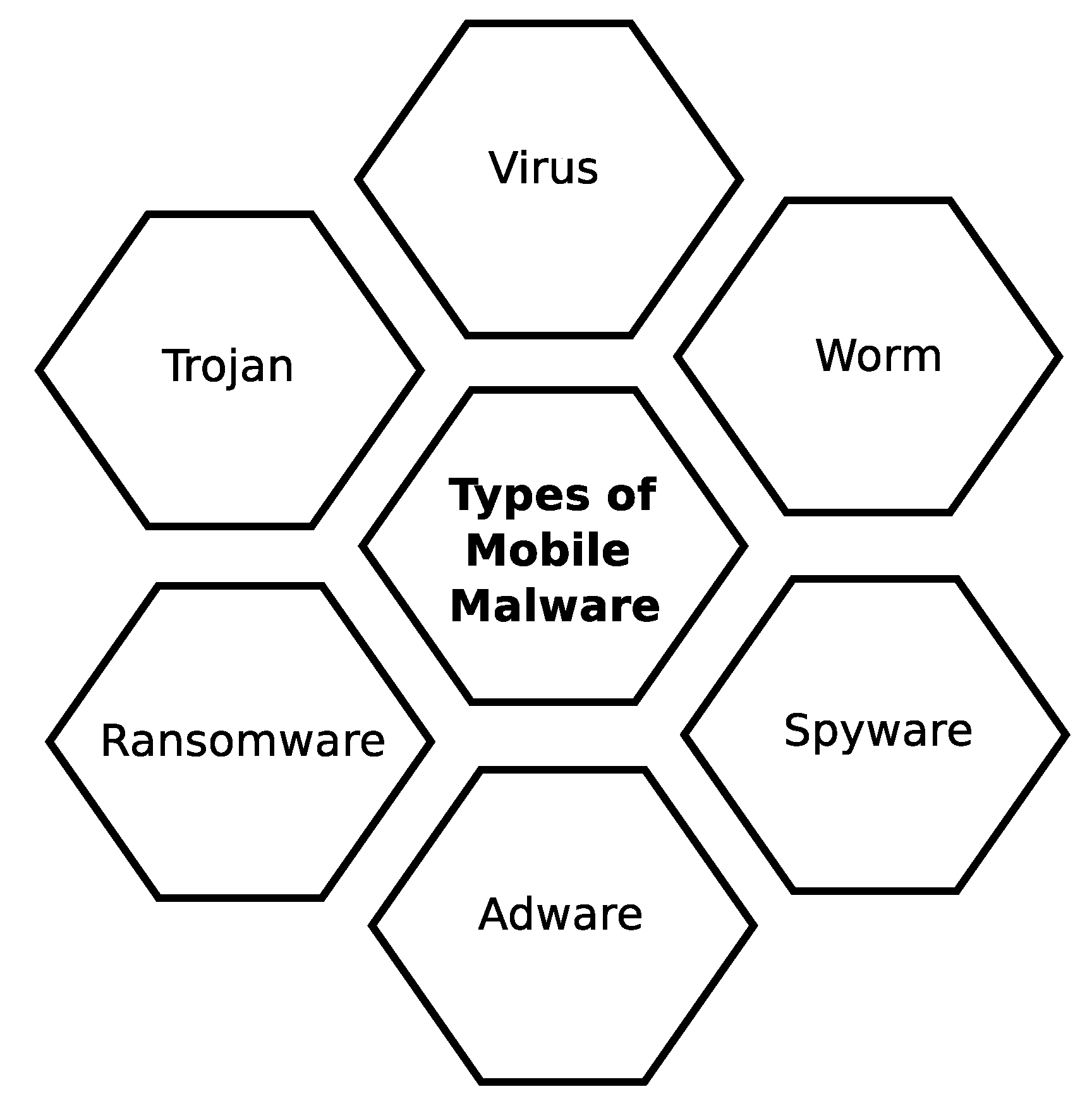
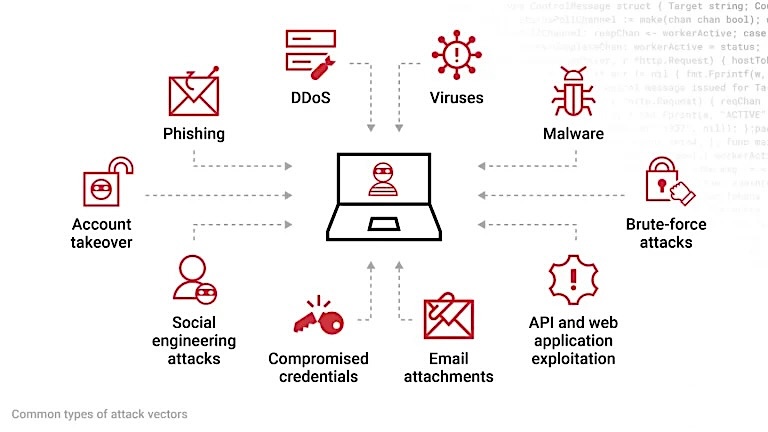
Malware threats are a constant concern for Windows users. From ransomware to spyware, malicious software can steal your data, damage your files, or cripple your PC. Fortunately, Windows systems come equipped with robust protection features, and with the right configuration, you can greatly minimize your risk. In this article, we will walk through actionable, step-by-step strategies to help you secure your Windows system against malware threats using the G Network configuration. We will cover the essential settings and techniques to ensure comprehensive malware protection.Understanding the G Network Configuration
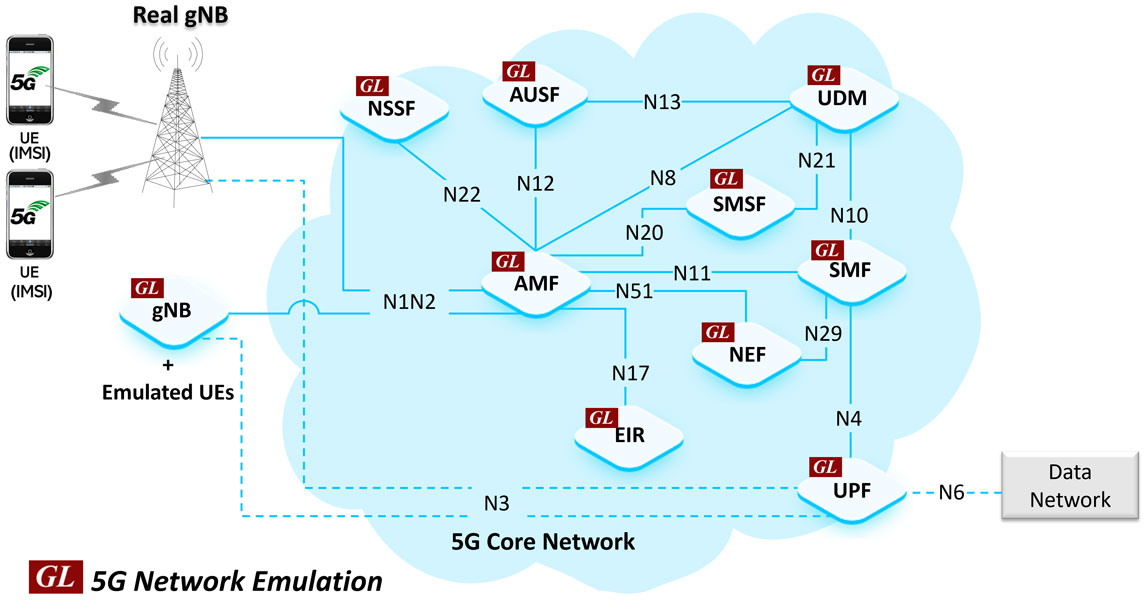
The G Network configuration is a set of policies and settings that work together to provide robust malware protection. This configuration is designed to extend the malware and social engineering protection offered by Windows Defender to cover network traffic and connectivity on your organization's devices.Step 1: Configure Windows Defender
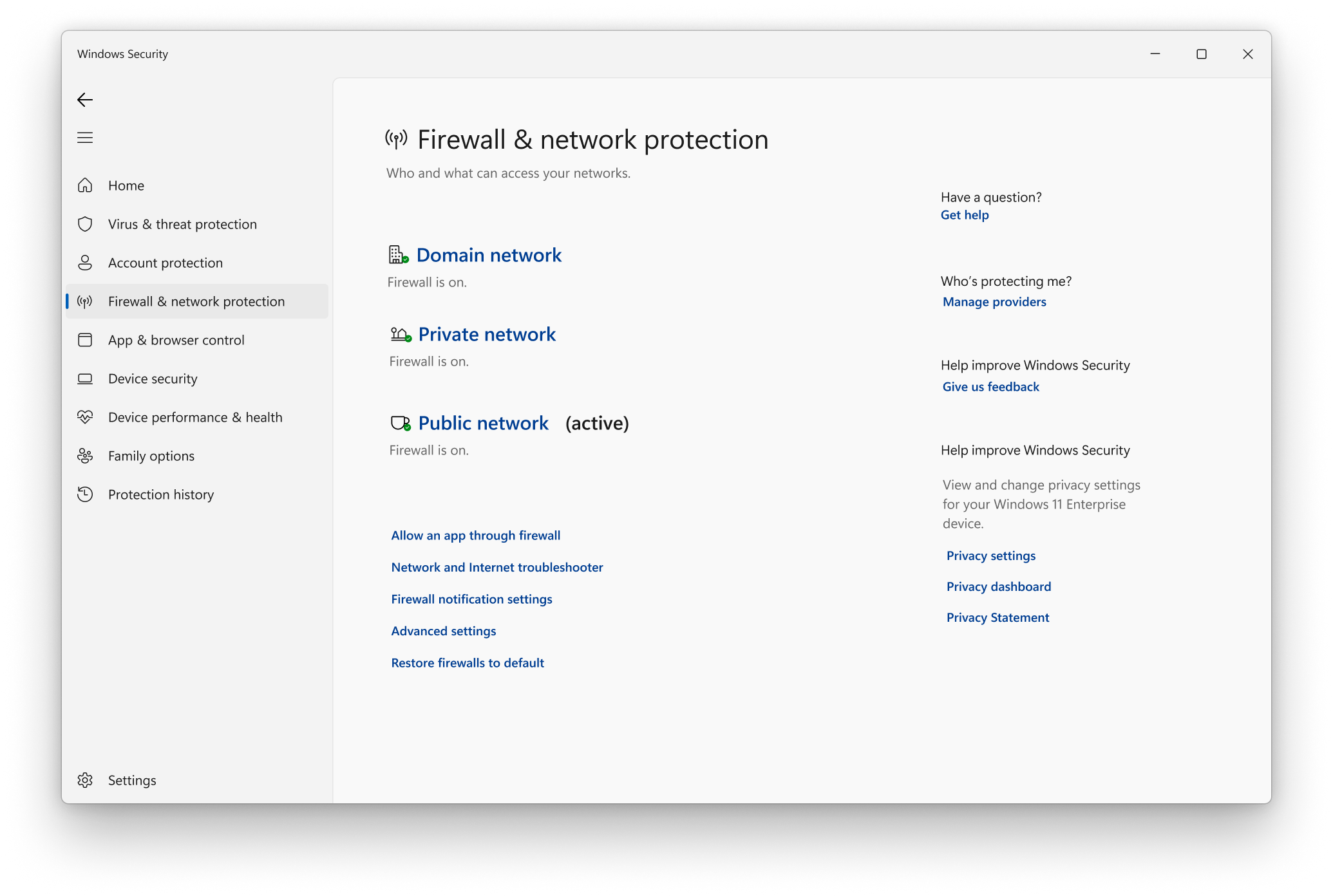
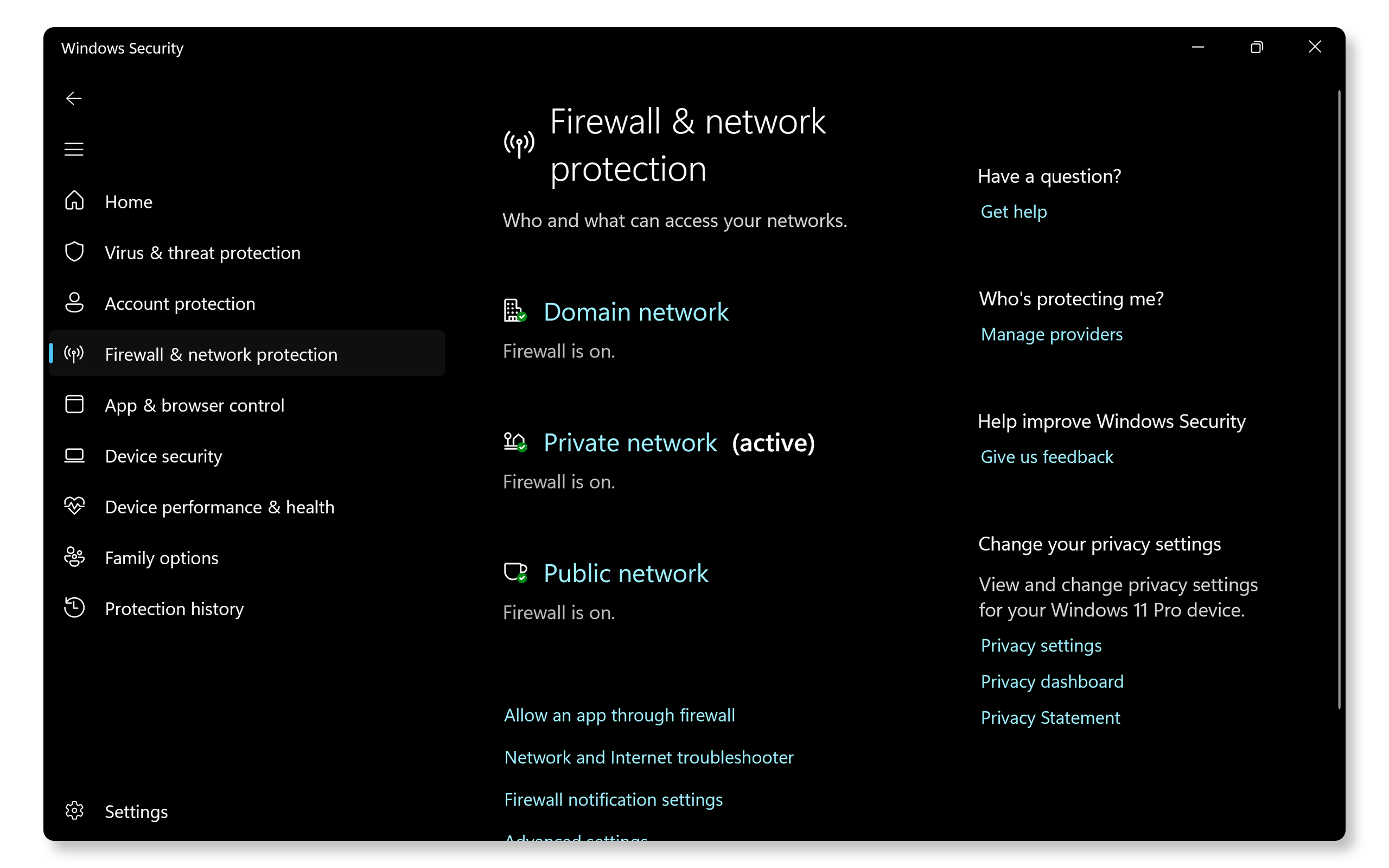
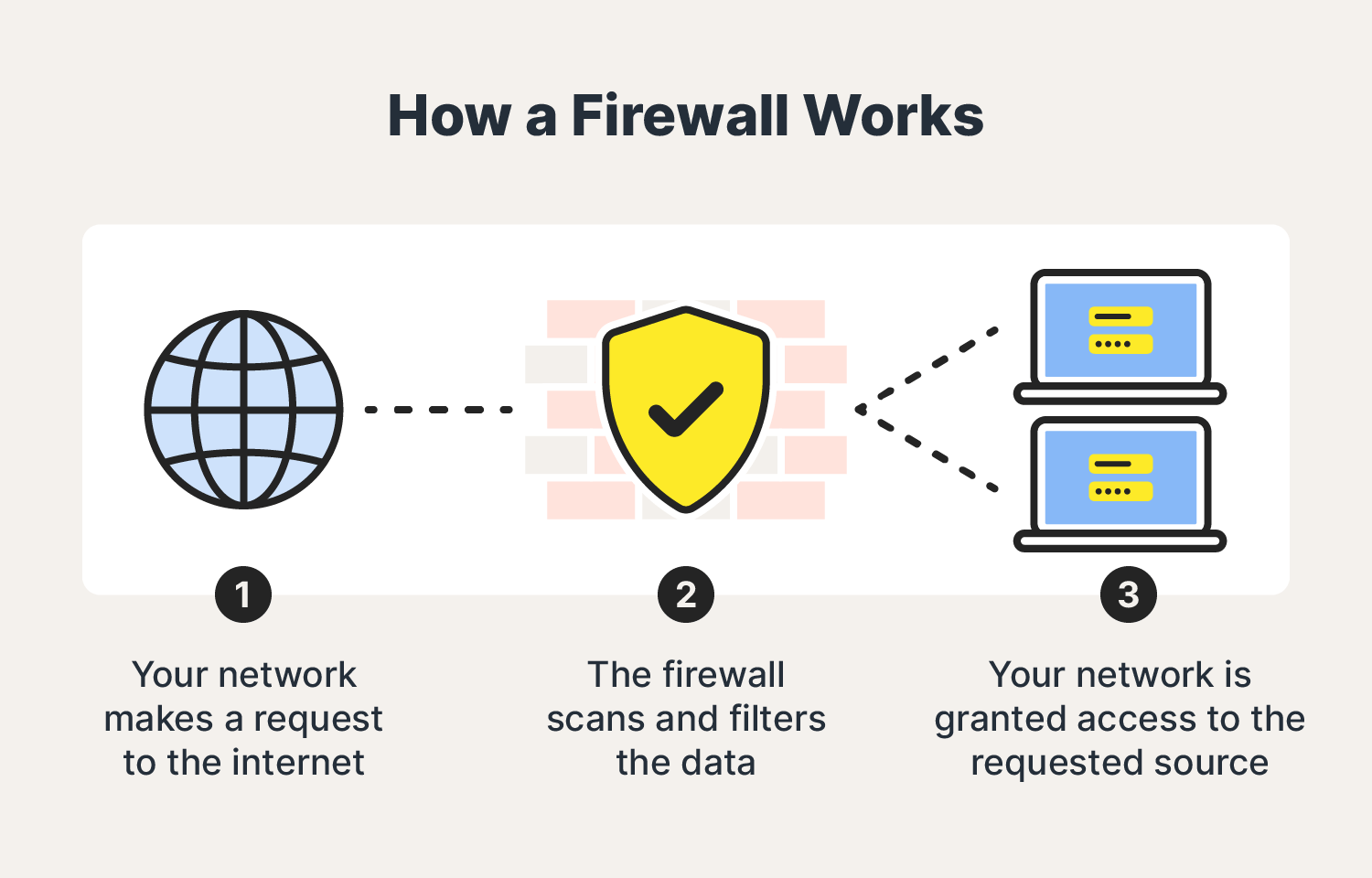
To start configuring the G Network for malware protection, you need to enable Windows Defender. Here's how: * Open the Windows Defender Firewall settings by searching for "Firewall" in the Start menu and selecting "Windows Defender Firewall with Advanced Security." * Click on the "Inbound Rules" tab and then click on the "New Rule" button. * Select "Rule Type" as "Port" and click "Next." * Choose "TCP" and specify the ports that you want to allow incoming traffic on. Click "Next." * Select "Allow the connection" and click "Next." * Give the rule a name and click "Finish."Step 2: Configure Network Protection
To enable network protection, you need to create a Group Policy Object (GPO) and configure the settings for network protection. * Open the Group Policy Editor by searching for "Group Policy Editor" in the Start menu. * Create a new GPO or edit an existing one. * Go to Computer Configuration > Administrative Templates > Windows Components > Microsoft Defender Antivirus > Microsoft Defender Exploit Guard > Network Protection. * Configure the settings for network protection by enabling the policy and selecting the network types that you want to protect.Step 3: Configure Malware Detection



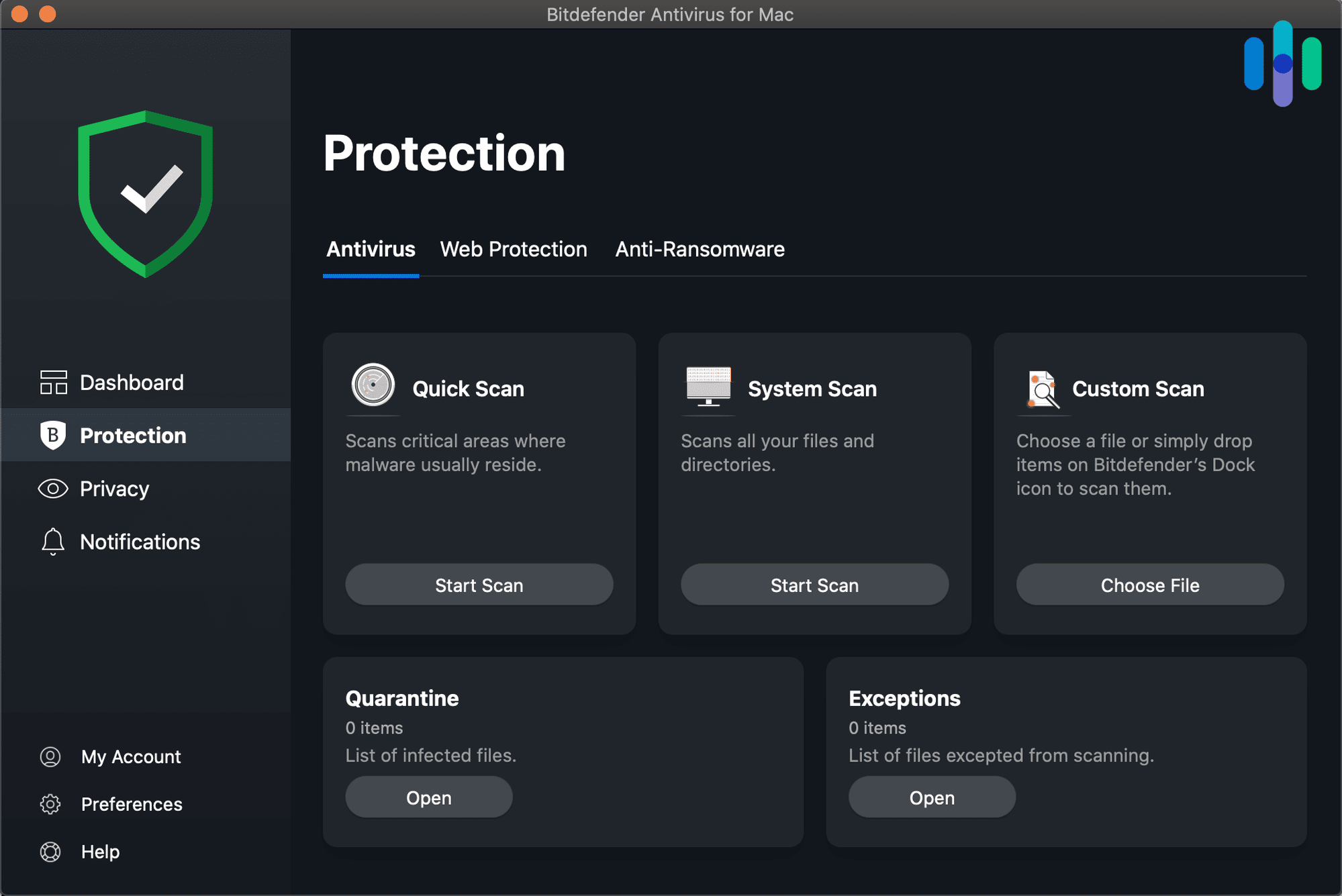

:max_bytes(150000):strip_icc()/avira-free-security-windows-7b5f7a644cd24b6786da48b66e7761b4.png)