Setting Up a G Wifi Network for Virtual Private Network Concentrator
In today's digital landscape, securing your network is more crucial than ever. With the increasing number of remote workers and branch offices, virtual private networks (VPNs) have become an essential tool for businesses to ensure secure and efficient communication. Among the various VPN options, a virtual private network concentrator (VPN concentrator) has emerged as a reliable solution for organizations seeking to protect their data and infrastructure. In this article, we will explore the concept of VPN concentrators and provide a comprehensive guide on setting up a G Wifi network for a VPN concentrator.
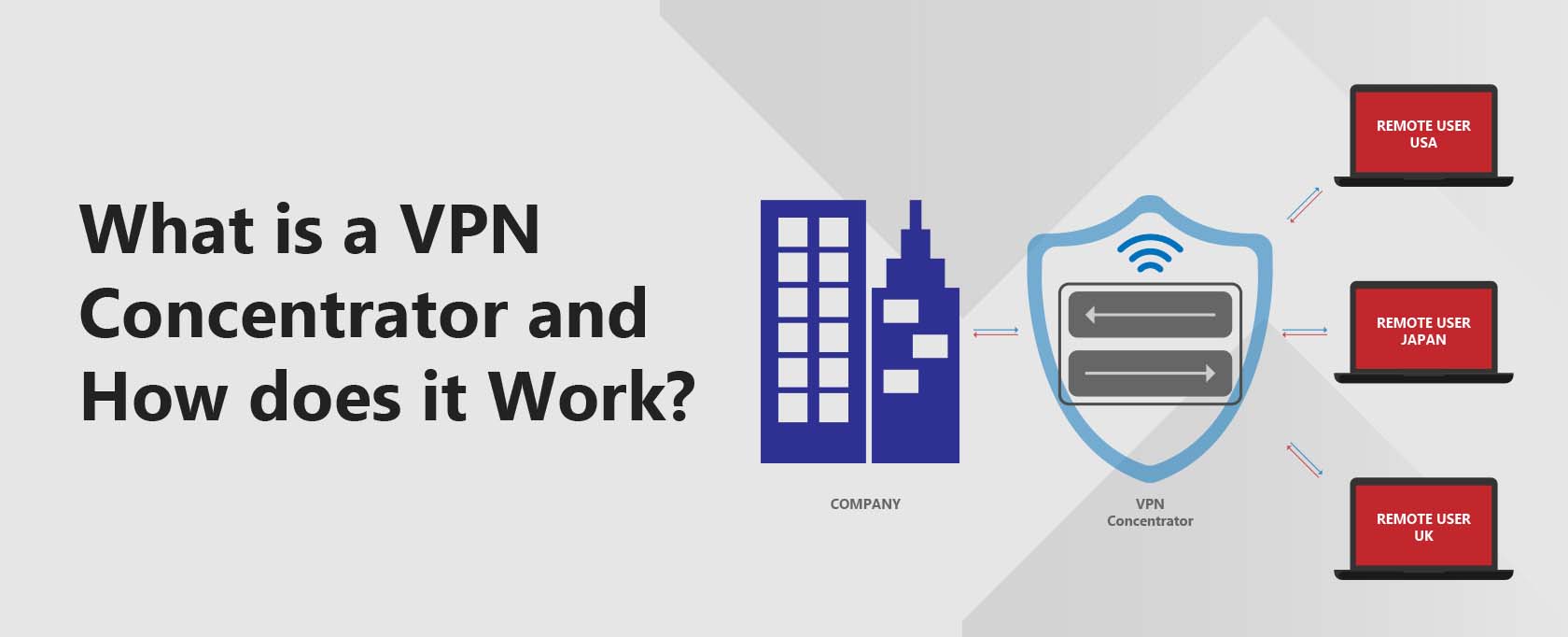
What is a Virtual Private Network Concentrator?
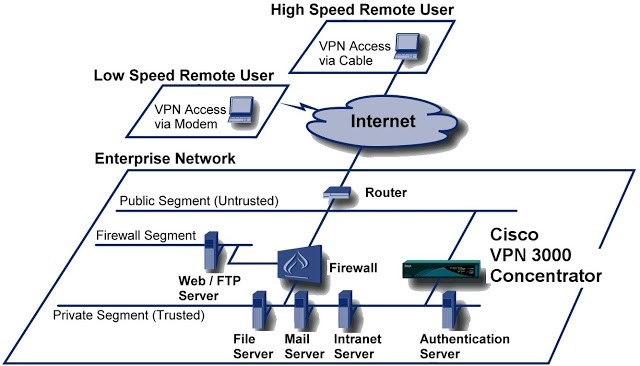
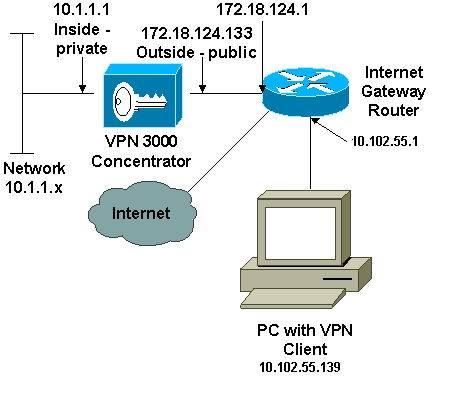
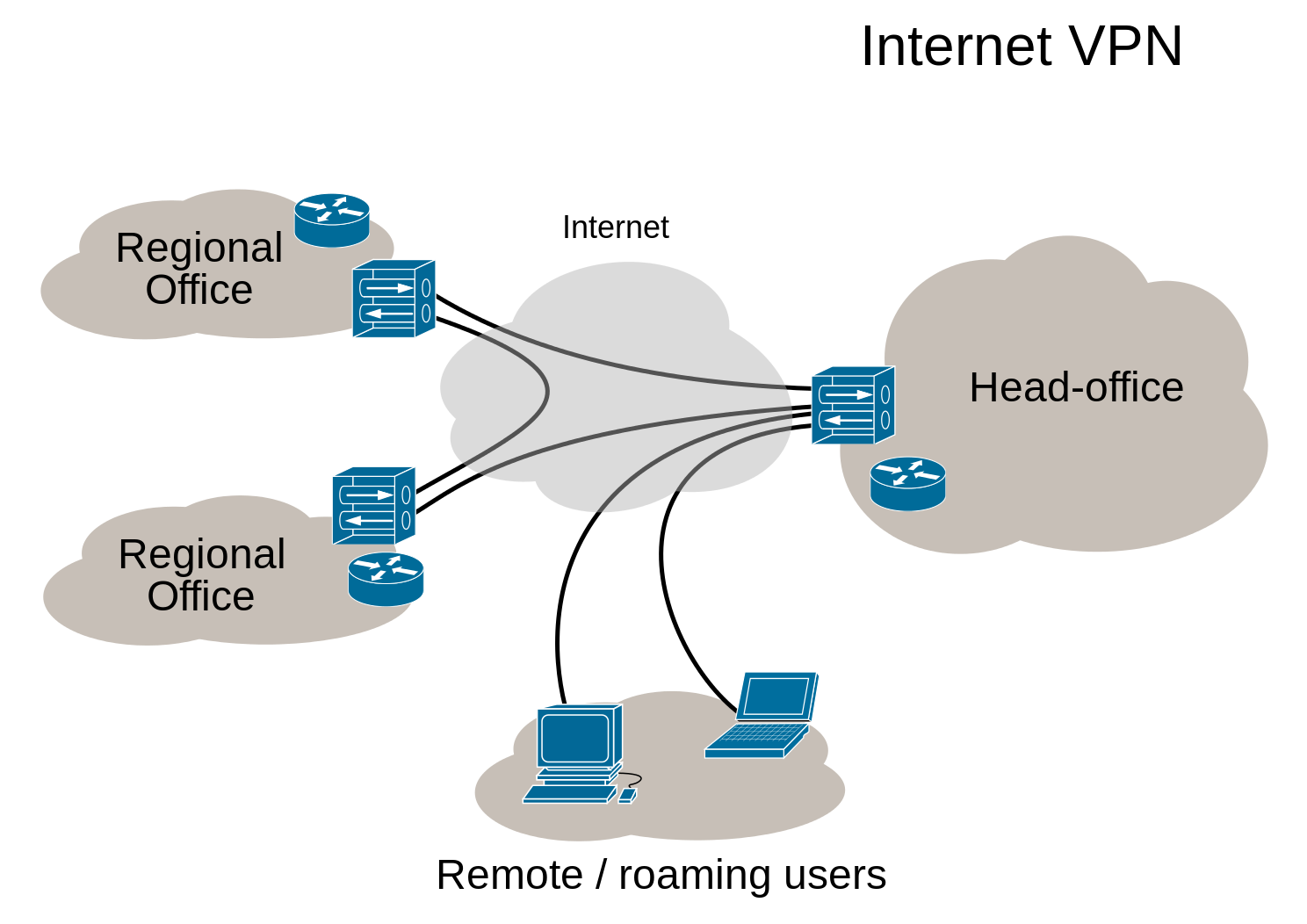
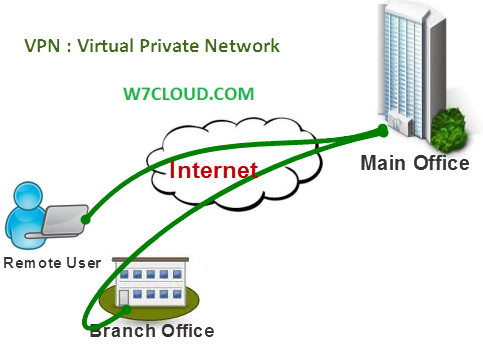
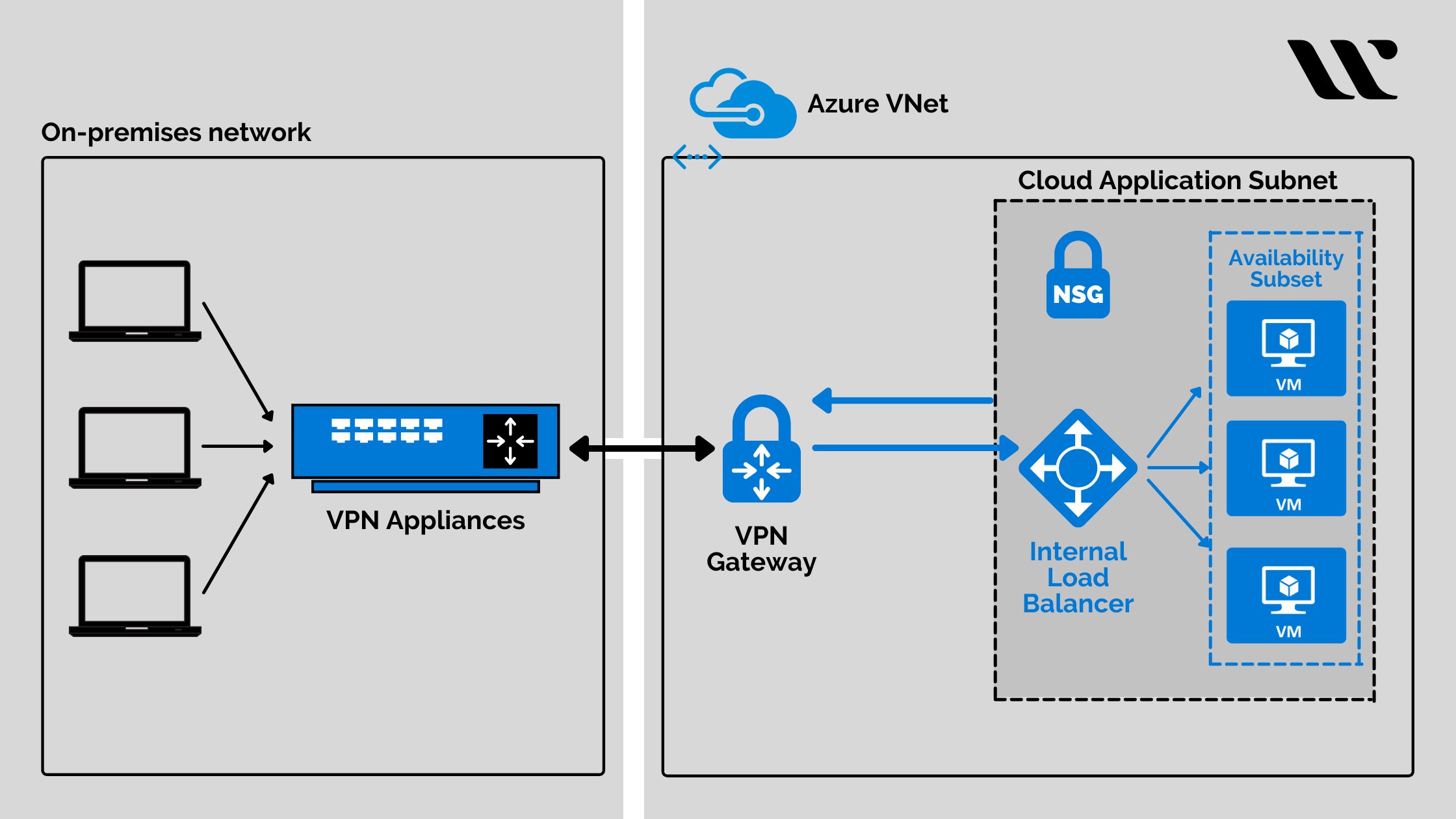
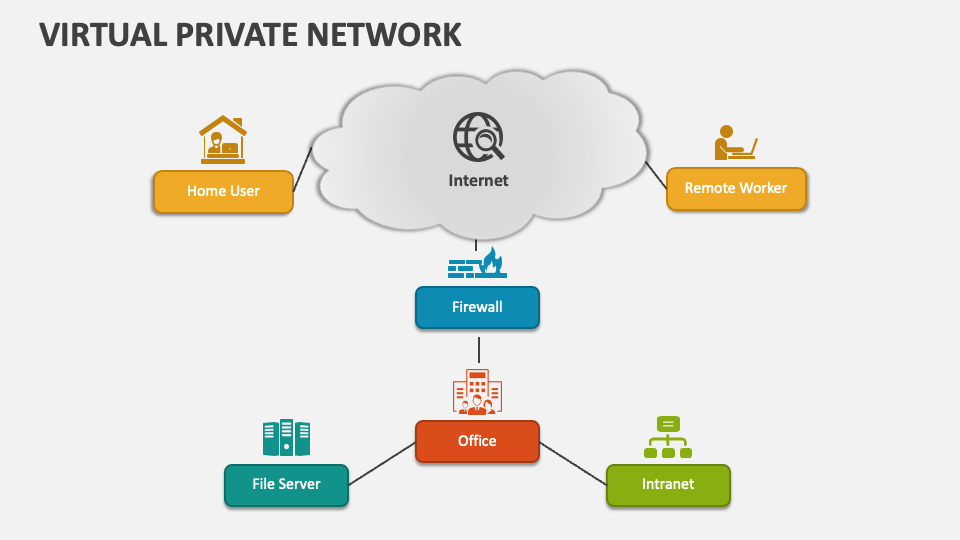
A VPN concentrator is a powerful networking device that allows multiple VPN connections to merge into a single network. Its primary function is to securely connect remote workers or branch offices to a private network over the internet by establishing a secure tunnel with encryption. The concentrator consolidates VPN connections from multiple remote users and devices onto a single device, making the connection more efficient and manageable.
Benefits of a VPN Concentrator
- Security: VPN concentrators encrypt data, ensuring that sensitive information is protected from unauthorized access.
- Scalability: VPN concentrators can handle multiple connections, making them ideal for large organizations with numerous remote users.
- Efficiency: By consolidating multiple VPN connections onto a single device, VPN concentrators reduce network congestion and improve overall performance.
- Flexibility: VPN concentrators can accommodate various types of VPNs, including site-to-site, remote access, and extranet VPNs.
Setting Up a G Wifi Network for a VPN Concentrator
To set up a G Wifi network for a VPN concentrator, follow these steps:
Step 1: Plan Your Network Infrastructure
Before setting up your G Wifi network, it's essential to plan your infrastructure. Determine the number of remote workers, the type of VPNs you need, and the level of security required. This will help you choose the right VPN concentrator and configure your network accordingly.
Step 2: Choose a VPN Concentrator
Choose a VPN concentrator that meets your organization's needs. Consider factors such as scalability, security, and ease of use. Some popular VPN concentrators include those from Cisco, Juniper, and Vyatta.
Step 3: Configure the VPN Concentrator
Configure the VPN concentrator according to your organization's needs. This includes setting up the VPN connection, configuring the encryption method, and establishing access control lists (ACLs). Ensure that the concentrator is compatible with your G Wifi network.
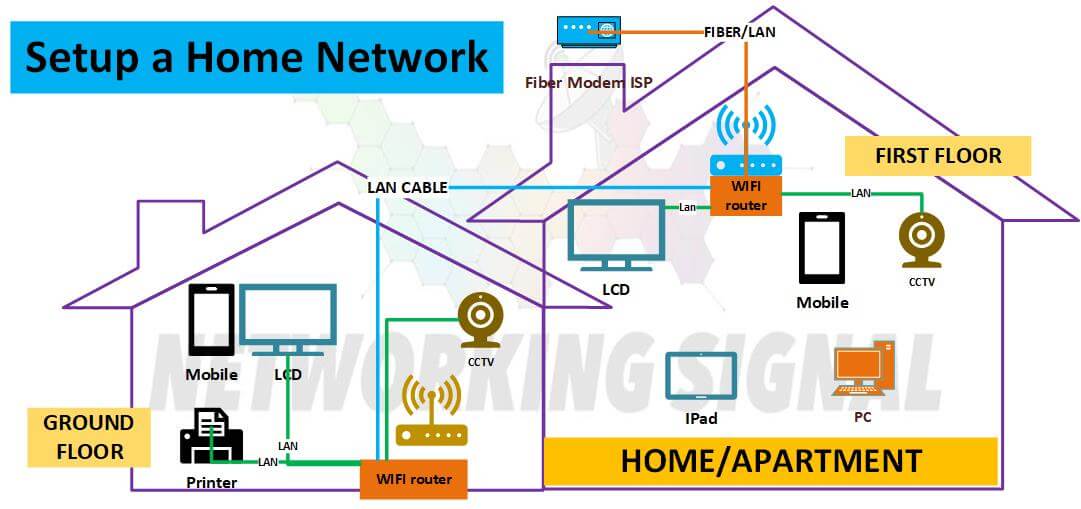
Step 4: Set Up the G Wifi Network
Set up your G Wifi network to accommodate the VPN concentrator. This includes configuring the access points, setting up the network topology, and ensuring that the VPN concentrator is properly integrated with the network.
Step 5: Test and Monitor the VPN Concentrator
Test and monitor the VPN concentrator to ensure that it is functioning correctly. Verify that the VPN connections are stable, and data is being encrypted and decrypted correctly.
Conclusion
Setting up a G Wifi network for a VPN concentrator is a complex process that requires careful planning and configuration. By following these steps, you can ensure a secure and efficient VPN connection for your organization. Remember to choose the right VPN concentrator, configure it according to your needs, and test and monitor the setup to ensure that it is working correctly. With a well-implemented VPN concentrator, you can enjoy the benefits of secure, scalable, and efficient network communication.