G Wireless Network Security Audit and Setup: A Comprehensive Guide
In today's hyper-connected world, wireless networks have become the backbone of modern business operations. Yet, they're often the weakest link in your cybersecurity chain. A G Wireless Network Security Audit and Setup is crucial to identifying and fixing potential vulnerabilities in your wireless network, protecting sensitive data, and creating a more resilient IT environment.
What is a G Wireless Network Security Audit and Setup?
A G Wireless Network Security Audit and Setup is the process of evaluating Wi-Fi networks to identify security weaknesses, configuration flaws, and potential vulnerabilities that attackers could exploit. It involves assessing the security, effectiveness, and performance of your wireless network to get a real in-depth review into its condition.
Importance of a G Wireless Network Security Audit and Setup
Ensuring your network's security is essential to avoiding financial and reputational damage. A G Wireless Network Security Audit and Setup systematically identifies vulnerabilities, protects sensitive data, and creates a more resilient IT environment. By following a comprehensive checklist, organizations can systematically evaluate their wireless networks, from infrastructure assessment to compliance review.
Benefits of a G Wireless Network Security Audit and Setup
- Identifies security weaknesses and vulnerabilities
- Protects sensitive data and creates a more resilient IT environment
- Enhances the overall security posture of your organization
- Helps you stay compliant with regulatory requirements
- Provides a comprehensive review of your wireless network infrastructure
Steps to Perform a G Wireless Network Security Audit and Setup
To perform a G Wireless Network Security Audit and Setup, follow these steps:

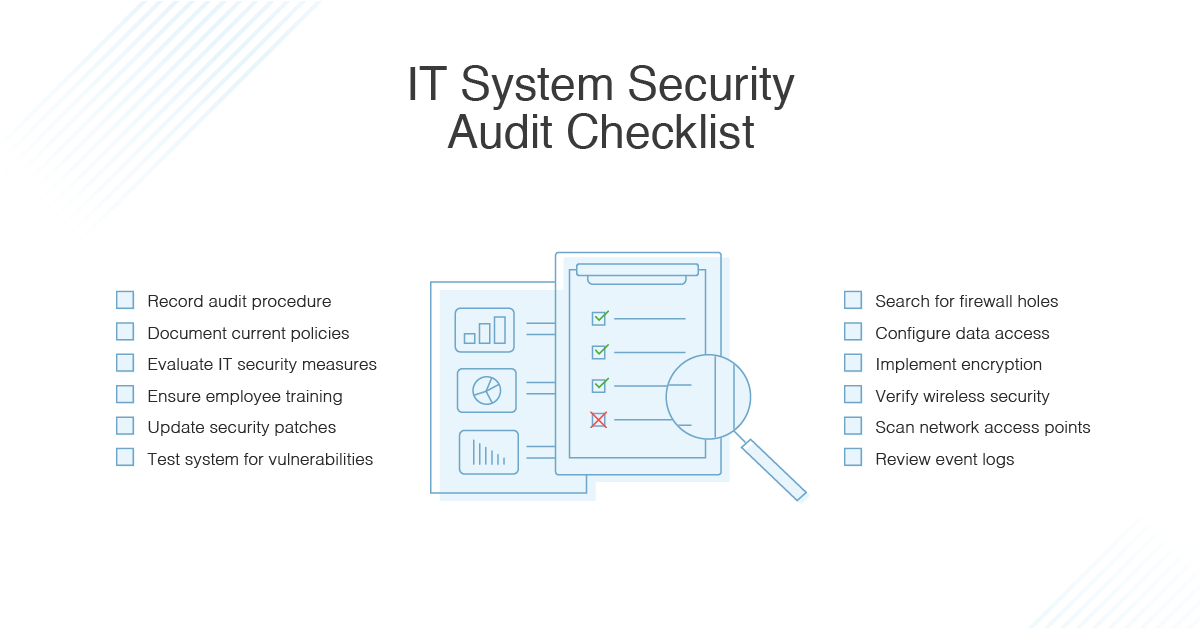
- Conduct a wireless network assessment to identify security weaknesses and vulnerabilities
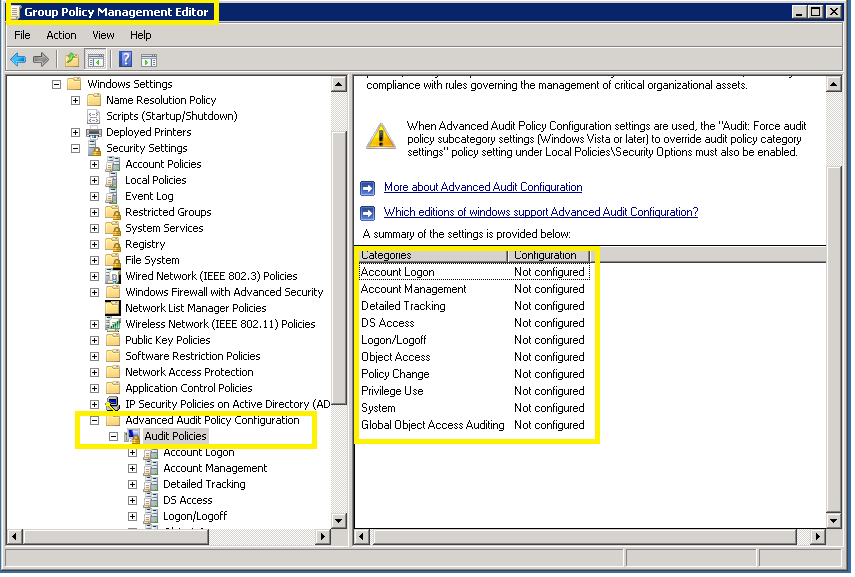
- Evaluate the security configuration of your wireless network, including access control, administration, logging, availability, client security, confidentiality, key management, physical security, policies, user authentication, and user awareness
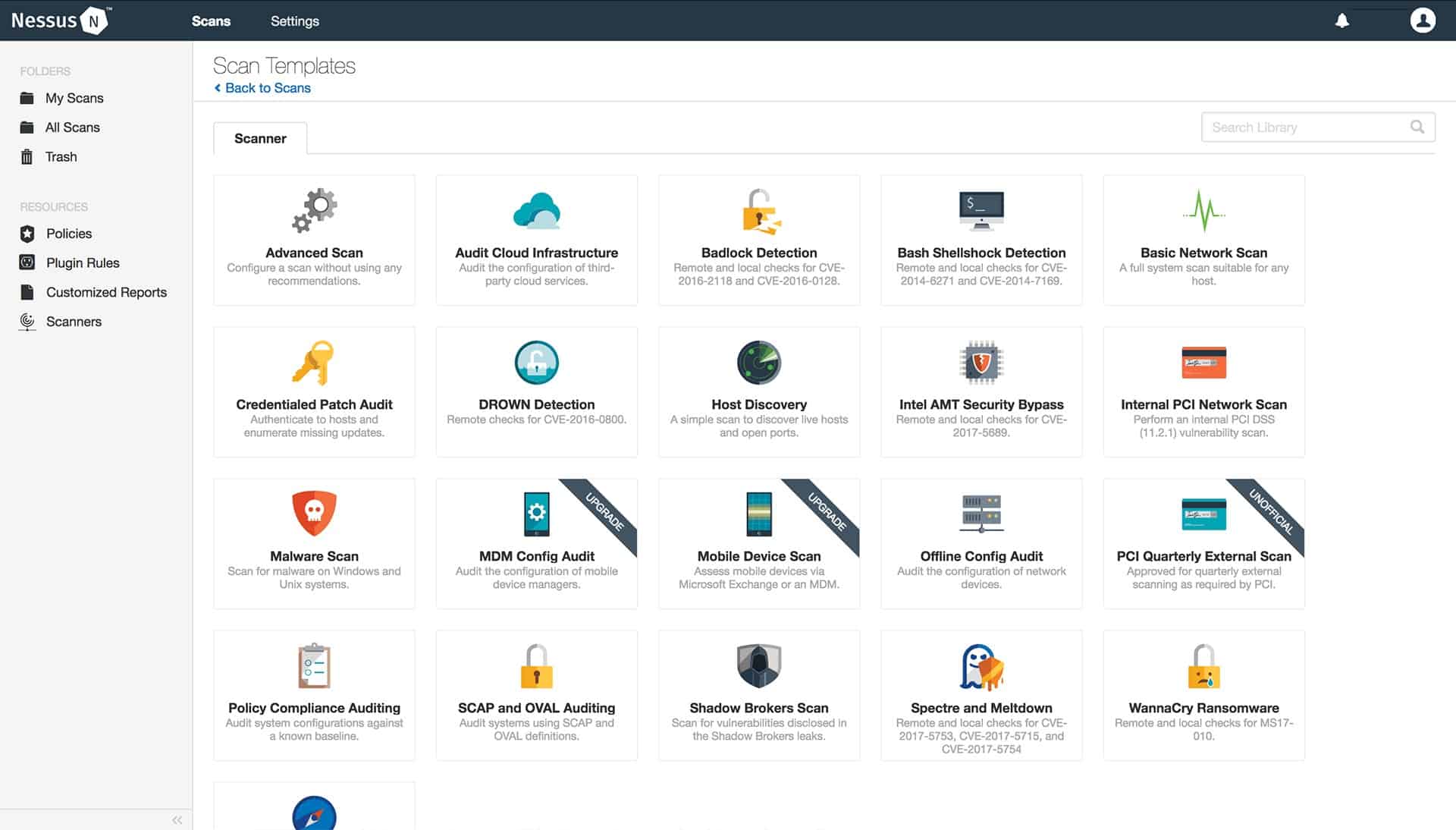
- Use tools such as Aircrack-ng, Wireshark, and Nmap to scan and test your wireless network
- Analyze the results of the audit and identify areas for improvement
- Implement recommendations to strengthen the security of your wireless network
- Monitor and maintain your wireless network to ensure ongoing security
Best Practices for a G Wireless Network Security Audit and Setup
To ensure the success of your G Wireless Network Security Audit and Setup, follow these best practices:
- Develop a comprehensive checklist to guide the audit process
- Use a combination of manual and automated tools to evaluate your wireless network
- Document all findings and recommendations
- Provide regular training and awareness programs for network administrators and users
- Regularly review and update your wireless network security policies
Conclusion
A G Wireless Network Security Audit and Setup is a critical step in maintaining the security, effectiveness, and performance of your wireless network. By following a comprehensive checklist and best practices, organizations can systematically evaluate their wireless networks, identify security weaknesses and vulnerabilities, and create a more resilient IT environment.
References
The following resources provide additional information on G Wireless Network Security Audit and Setup:
- SANS Institute: Enterprise Wireless Audit Checklist
- Auvik: Compliance Auditing Support
- Red Hat Ansible Automation Platform: Network Operations Automation
- CISA Directive: Mitigating Risks from End-of-Support Edge Devices
- IEEE 802.11: Wireless Local Area Network (WLAN) Technical Standards