G Network Security Setup for Incident Response: Protecting Your Organization's Assets
As the threat landscape continues to evolve, it's essential for organizations to have a robust incident response plan in place to protect their assets and minimize the impact of security breaches. A well-designed G Network Security Setup for Incident Response can help organizations detect, contain, and recover from cybersecurity threats, ensuring business continuity and maintaining stakeholder trust.
The Importance of an Effective Incident Response Plan
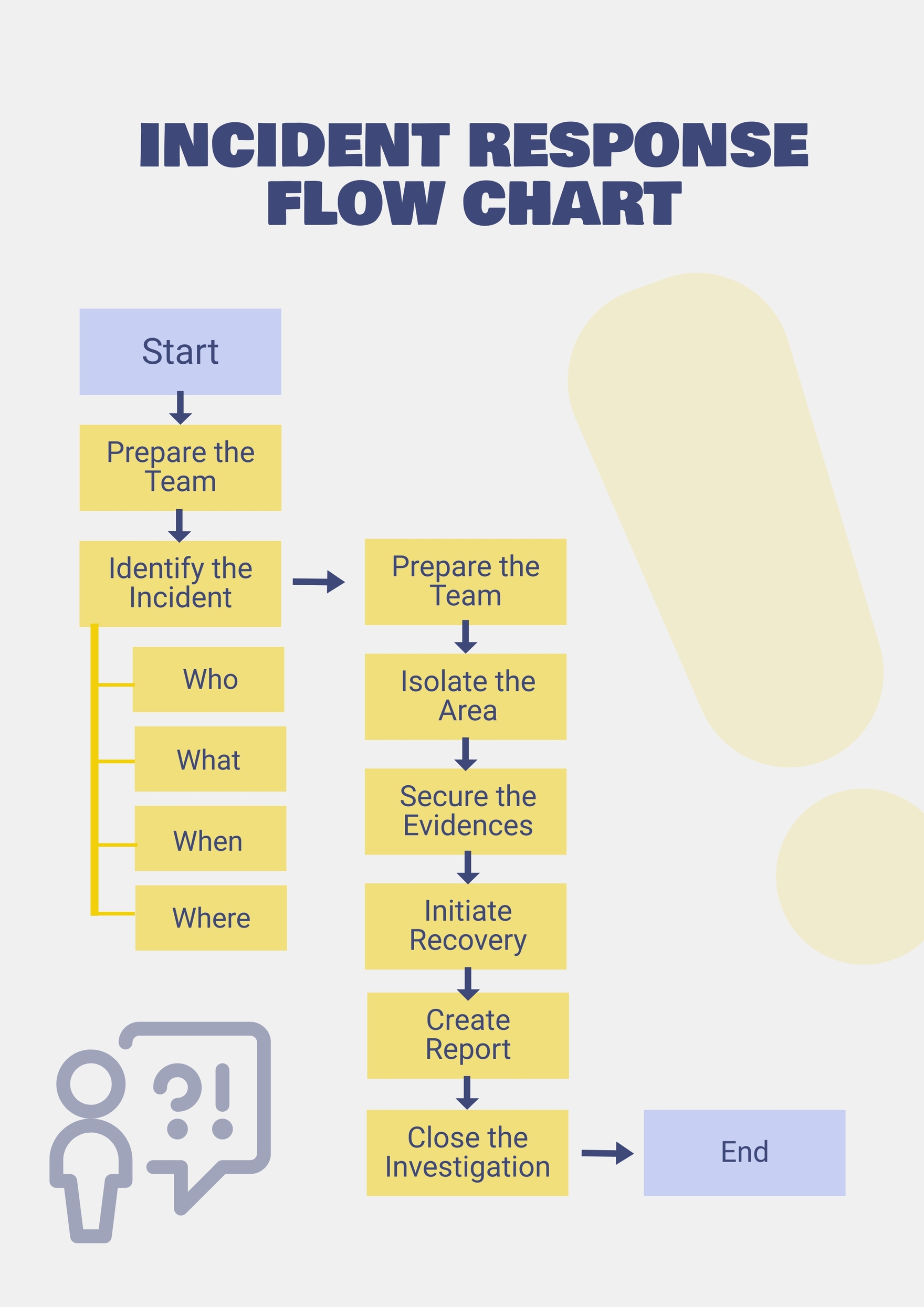
Developing an effective incident response plan is crucial for organizations to respond quickly and efficiently to security incidents. An incident response plan outlines the procedures and protocols for responding to security incidents, ensuring that individuals and teams are equipped to handle various scenarios. By having a clear plan in place, organizations can minimize the impact of security breaches, reduce the risk of data loss, and maintain stakeholder confidence.
Components of a Comprehensive Incident Response Plan
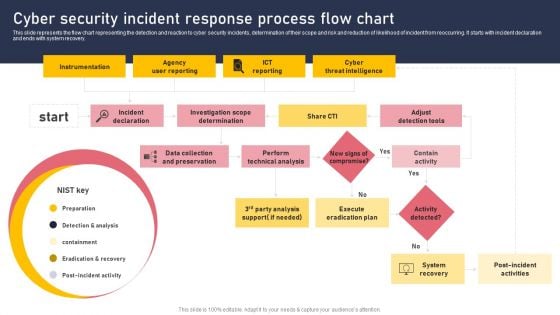
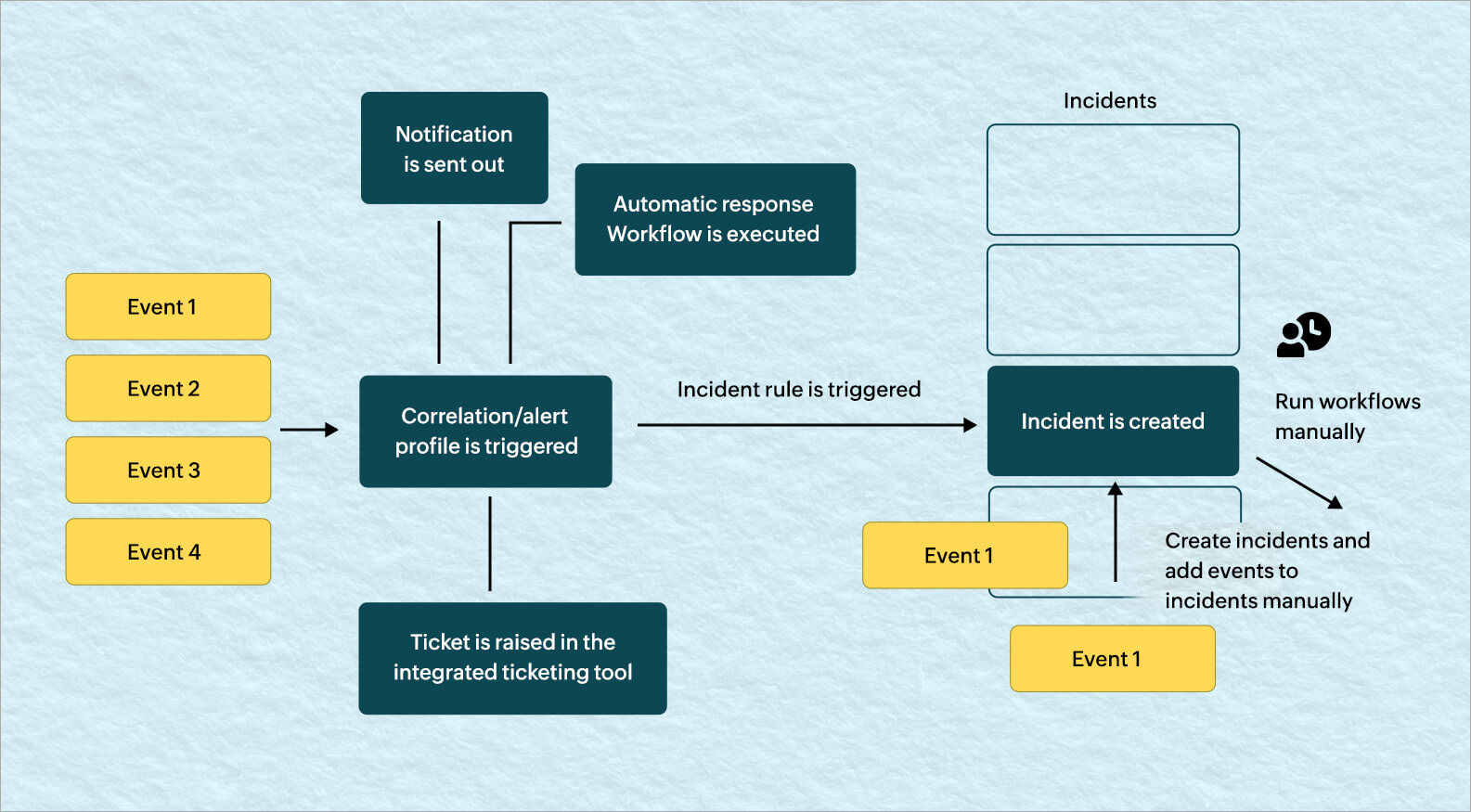
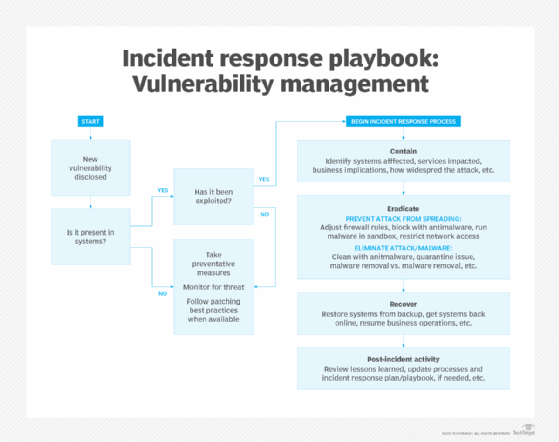
A comprehensive incident response plan should include the following components:
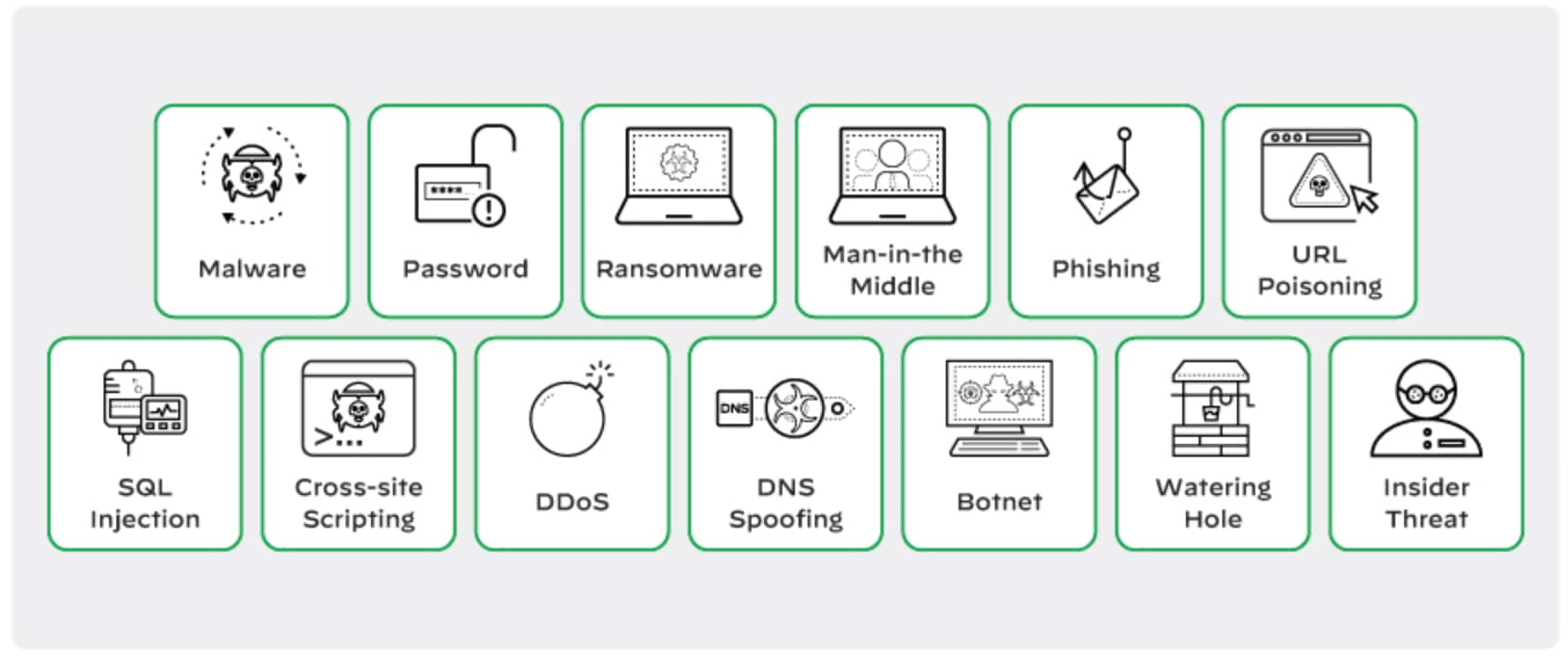
- Incident classification: A clear definition of what constitutes an incident and how it should be classified.
- roles and responsibilities: Clearly defined roles and responsibilities to ensure that everyone knows their part in incident response.
- Communication: Establishing communication channels and protocols to ensure prompt and effective communication during incidents.
- Incident containment: Procedures for containing and isolating the affected area to prevent further damage.
- Incident eradication: Strategies and procedures for removing the root cause of the incident.
- Post-incident activity: Procedures for handling post-incident activities, including lessons learned and remediation activities.

Best Practices for Implementing a G Network Security Setup for Incident Response
Implementing a G Network Security Setup for Incident Response requires careful planning, coordination, and practice. Here are some best practices to consider:
- Develop a comprehensive incident response plan that includes procedures for detection, containment, eradication, and post-incident activity.
- Establish clear roles and responsibilities to ensure that everyone knows their part in incident response.
- Conduct regular training and exercises to ensure that individuals and teams are prepared to respond to various scenarios.
- Implement a incident classification system to ensure that incidents are properly classified and responded to.
- Establish effective communication channels and protocols to ensure prompt and effective communication during incidents.
- Conduct regular reviews and updates of the incident response plan to ensure that it remains effective and relevant.
Conclusion
Developing a G Network Security Setup for Incident Response is crucial for organizations to protect their assets and minimize the impact of security breaches. By having a clear plan in place, organizations can respond quickly and efficiently to security incidents, ensuring business continuity and maintaining stakeholder trust. By following the best practices outlined in this article, organizations can implement a robust incident response plan that protects their assets and prepares them for various scenarios.