Securing Your Network: A Comprehensive Guide to G Router Firewall Rules Setup
Introduction
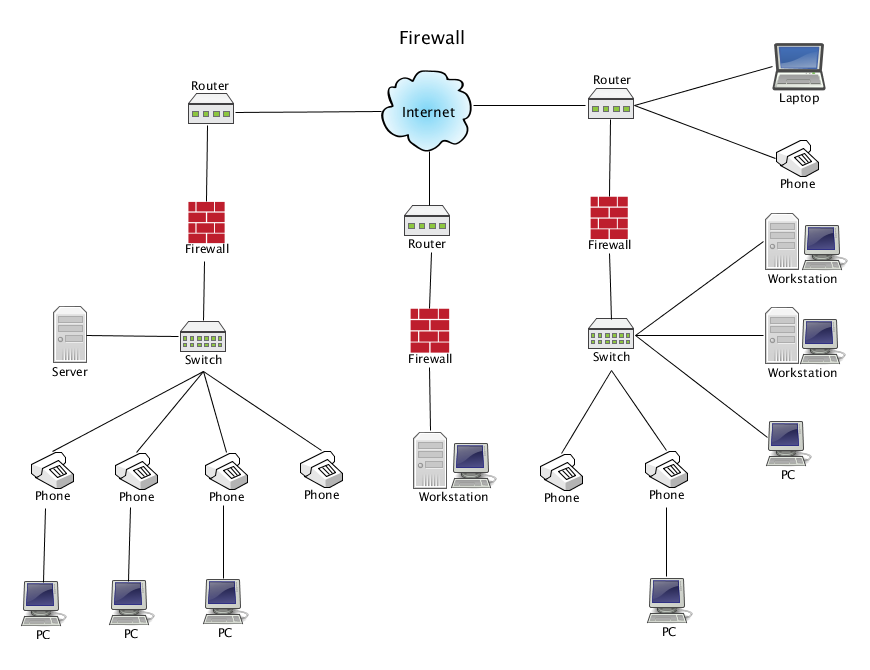
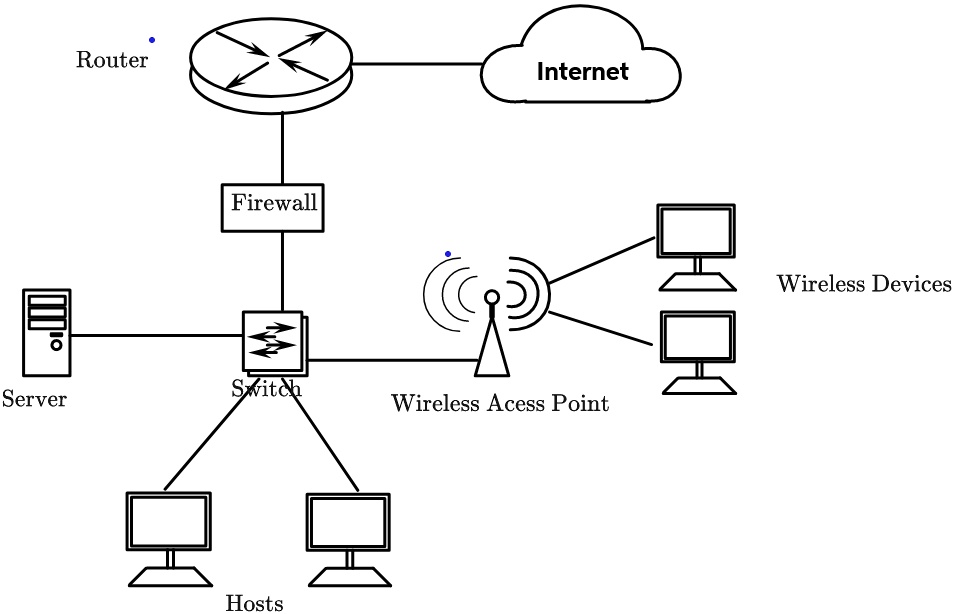
In today's digital age, network security is more critical than ever. With the increasing number of cyber threats and data breaches, it's essential to have a robust firewall setup to protect your network from potential risks. A G Router Firewall Rules Setup is a vital component of your network security arsenal, and in this article, we'll guide you through the process of setting up and configuring your router's firewall rules effectively.Understanding the Importance of Firewall Rules
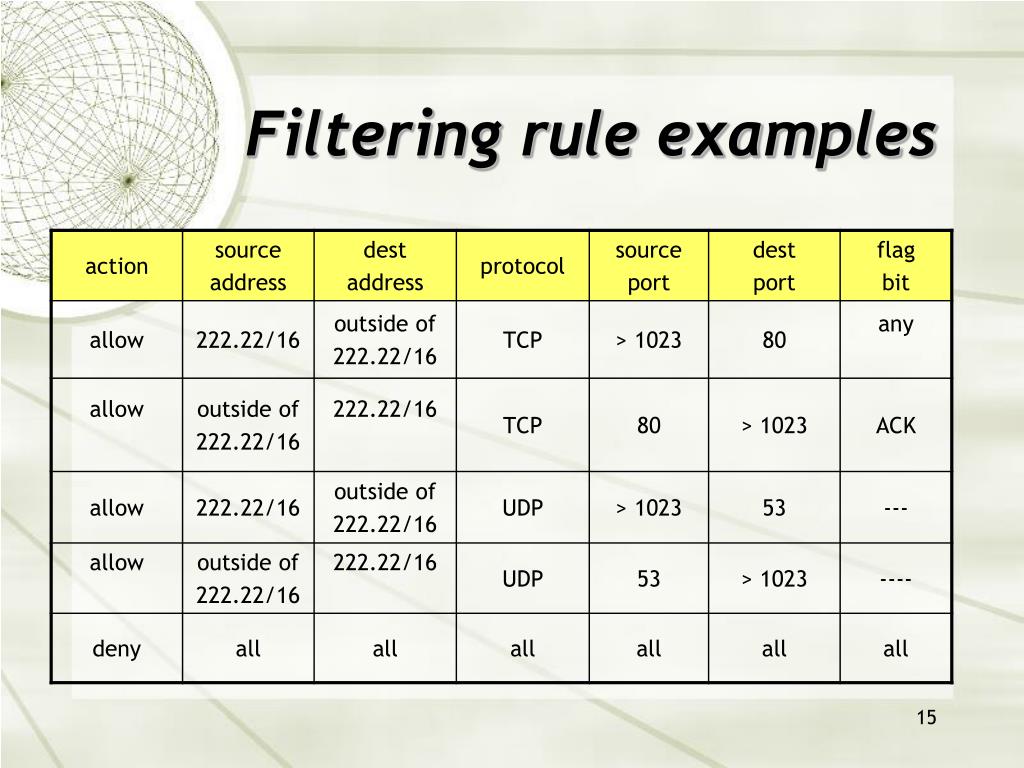
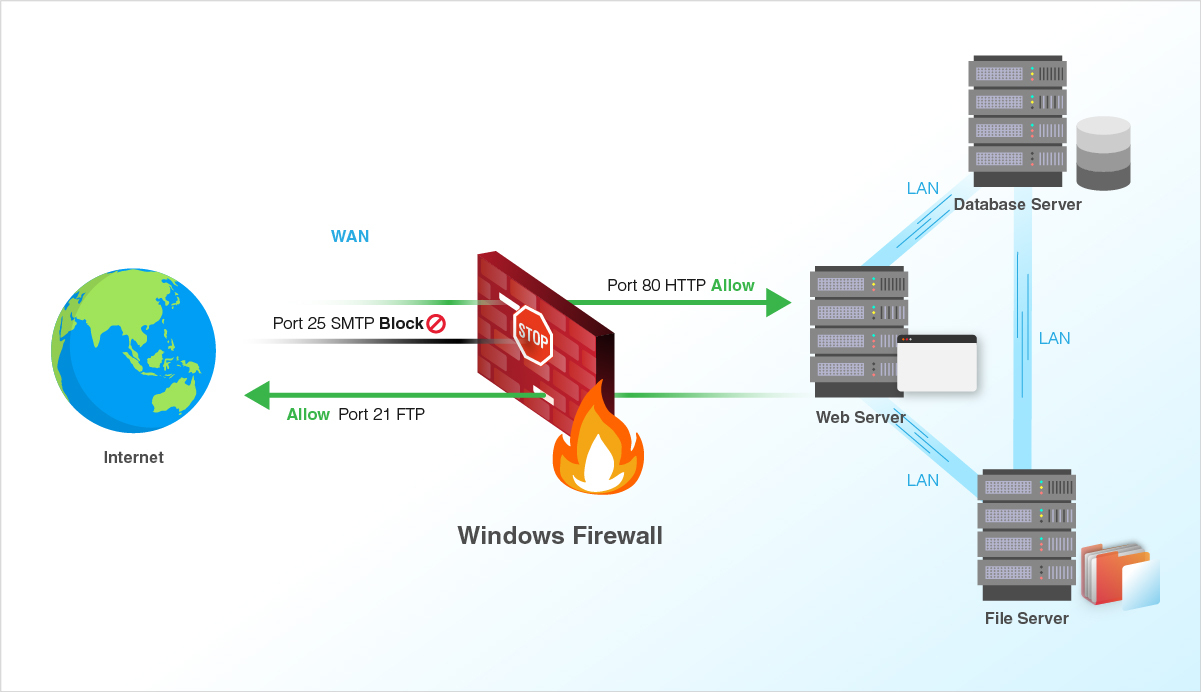
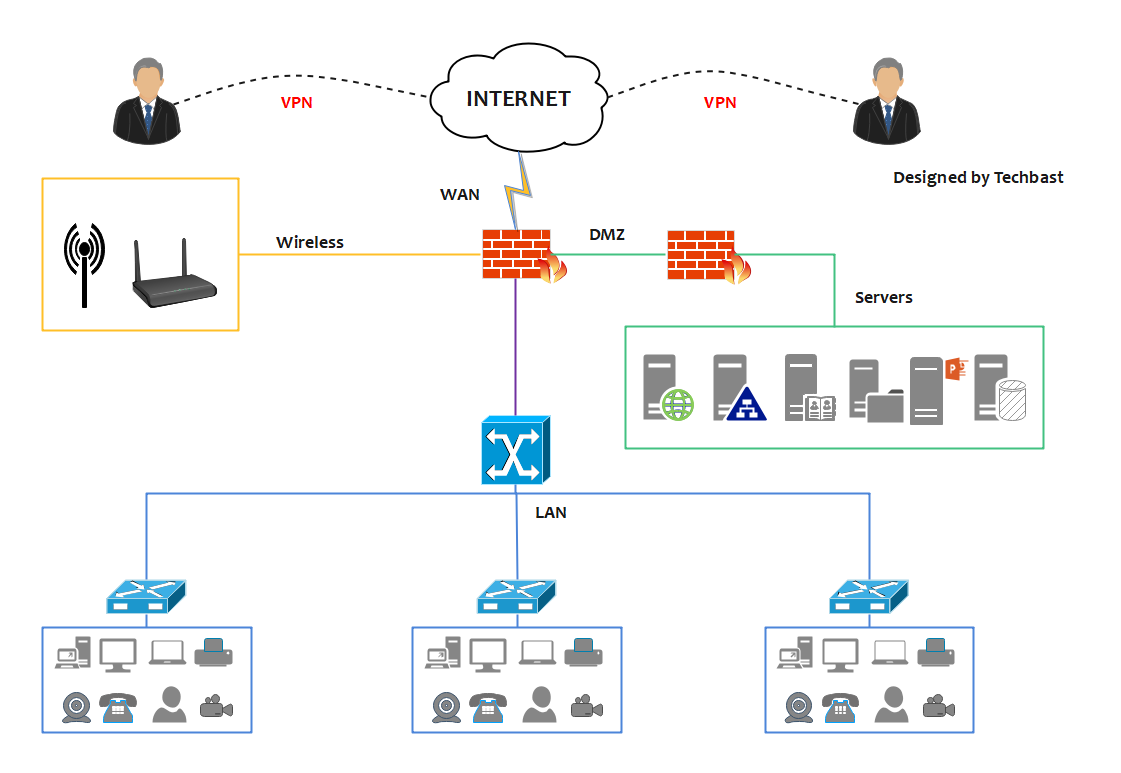
A firewall is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. Firewall rules are the foundation of a robust security strategy, and they play a crucial role in protecting your network from unauthorized access, malware, and other cyber threats. In this article, we'll focus on G Router Firewall Rules Setup, but the principles and concepts discussed can be applied to other routers and firewall systems.Accessing and Configuring Your Router's Firewall
To configure your router's firewall, you'll need to access your router's web-based interface. This is usually done by typing the router's IP address in a web browser, followed by the default login credentials. Once you're logged in, navigate to the firewall settings page, which is often found under the "Advanced" or "Security" section.Types of Firewall Rules
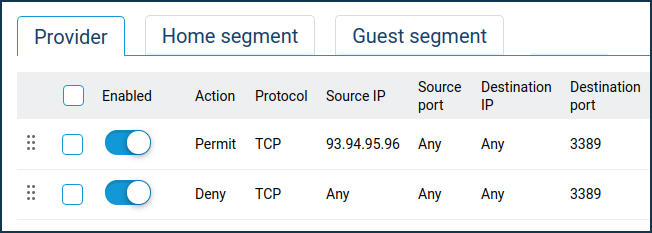
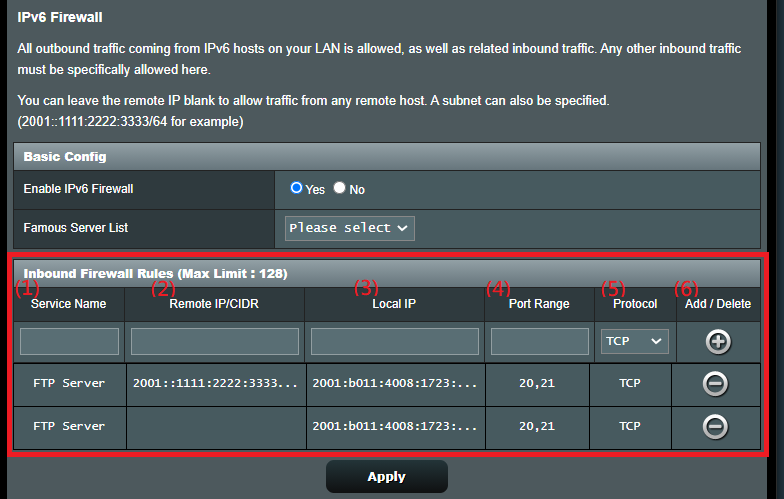
There are several types of firewall rules, including: * **Port Forwarding**: This rule allows incoming traffic to a specific port on your router, which is often used for online gaming, web servers, or other applications that require incoming traffic. * **Open Ports**: This rule opens a specific port on your router, allowing incoming traffic to reach the device associated with that port. * **DMZ**: This rule sets a device in a DMZ (Demilitarized Zone), which allows it to receive incoming traffic without filtering.Configuring Firewall Rules
To configure firewall rules, follow these steps: 1.Step 1: Access the Router's Web-Based Interface
Access your router's web-based interface by typing the router's IP address in a web browser and logging in with the default login credentials. 2.Step 2: Navigate to the Firewall Settings Page

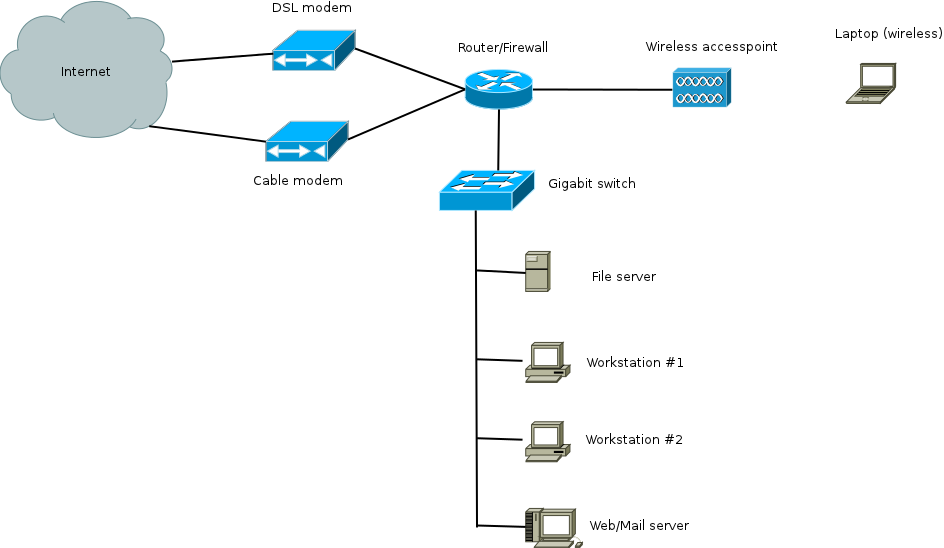


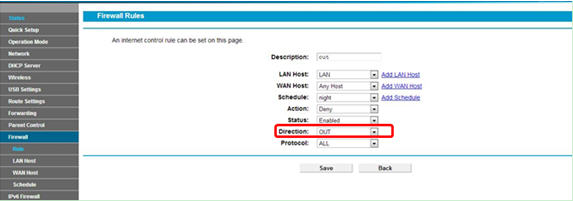
![[OpenWrt Wiki] Firewall Builder: Shorewall-lite [OpenWrt Wiki] Firewall Builder: Shorewall-lite](https://www.redswitches.com/wp-content/uploads/2023/05/firewall-working-1024x687.jpg)